Table of Contents
Why teams seek Frontegg alternatives
Frontegg is a customer identity platform designed for both B2B and B2C use cases. It provides authentication, user management, and embedded admin portals to help teams add enterprise-grade identity features such as SSO, multi-tenancy, and role-based access controls.
For many teams, Frontegg offers a strong starting point, especially when building products that need out-of-the-box enterprise capabilities. However, as applications grow and identity requirements become more complex, developers often encounter limitations around flexibility, customization, pricing, and operational scalability. There have also been reported instances of downtime.
Modern applications increasingly require fully customizable authentication journeys, seamless enterprise onboarding, flexible authorization models, and deep integration with broader application ecosystems. In these environments, opinionated abstractions and pre-built components can introduce friction rather than accelerate development.
Below, we break down the top reasons developers seek Frontegg alternatives, followed by a closer look at the leading identity platforms available today.
This guide will cover:
Why dev teams outgrow Frontegg
An overview of the top 6 Frontegg alternatives
A deep dive into each contender’s strengths and fit
A practical guide to finding the right Frontegg alternative
Why teams seek Frontegg alternatives
Many teams evaluate alternatives to Frontegg for several key reasons:
On a macro level, teams often run into challenges with flexibility, architecture, and enterprise readiness:
Limited flexibility: Frontegg’s opinionated abstractions can restrict customization, making it harder to support non-standard authentication flows, hybrid B2B/B2C use cases, or evolving product requirements without added complexity.
Limited control over user journeys: Hosted components and predefined flows can accelerate setup but restrict the ability to fully customize UX, branding, and experimentation across authentication experiences.
Multi-tenant limitations: While built for B2B SaaS, Frontegg can be difficult to adapt to more complex tenant models, such as multi-org users or cross-tenant roles, leading to additional engineering overhead.
Enterprise SSO and federation can also introduce friction as teams onboard larger customers:
Enterprise SSO complexity and cost: Setting up and managing SAML/OIDC connections, certificates, and tenant-specific configurations remains time-consuming, while SSO pricing can increase significantly as more enterprise customers are onboarded.
SSO migration and interoperability challenges: SSO implementations can be harder to migrate or standardize across providers, creating friction when switching platforms or onboarding enterprise customers with diverse identity providers.
Developer experience and extensibility are another common source of friction:
Developer experience friction: Rigid SDKs and abstractions can make it harder to debug, extend, or deeply customize authentication logic, slowing down development when teams need more control.
Integration and extensibility gaps: Integrating with third-party tools like fraud detection, analytics, or custom services may require additional effort, as extensibility is more limited compared to developer-first platforms.
As applications scale, operational complexity and costs often become more noticeable:
Operational overhead as teams scale: Managing tenants, roles, permissions, and SSO onboarding can become resource-intensive without strong automation or self-service capabilities, creating bottlenecks for growing teams.
Pricing at scale: Costs tied to enterprise features, admin portals, and SSO connections can grow quickly, prompting teams to look for more predictable and scalable pricing models.
Finally, reliability and support concerns can impact production environments:
Reliability concerns: Some teams report instances of downtime and service instability, which can impact authentication flows and create risk for customer-facing applications that depend on consistent uptime.
Support and responsiveness gaps: Developers have cited slow response times and difficulty resolving issues, leading to frustration when troubleshooting production incidents or implementing more complex identity scenarios.
Each alternative below addresses these challenges differently depending on your architecture, ecosystem, and developer workflow requirements.
Frontegg alternatives at a glance
Here’s how the top 6 Frontegg alternatives stack up:
Features | Strengths | Best for | |
|---|---|---|---|
Descope | Workflow-based auth, MFA, SSO, SCIM, RBAC/FGA, passwordless, APIs/SDKs | Flexible orchestration, self-service SSO, unified auth + authz, fast iteration | B2B SaaS, B2B2C apps, teams needing flexibility and scale |
Auth0 | Auth, MFA, SSO, RBAC, Actions/Rules, hosted login | Mature platform, large ecosystem, strong enterprise support | Enterprise apps needing broad identity coverage |
FusionAuth | Auth APIs, SSO, MFA, user management, flexible deployment | Self-hosted option, predictable pricing, full control | Teams prioritizing cost control and infrastructure ownership |
Amazon Cognito | User pools, federation, Lambda triggers, AWS integrations | Deep AWS integration, scalable, serverless extensibility | AWS-native applications |
Keycloak | SSO, federation, RBAC, LDAP/AD integration, open-source | No vendor lock-in, strong protocol support, extensible | Enterprises needing self-hosted identity and customization |
Ory | API-first auth (Kratos), OAuth2 (Hydra), fine-grained auth (Keto) | Modular architecture, maximum flexibility, open-source | Teams building custom,microservices-based identity systems |
Below, we’ll look more closely at what makes each one unique.
Descope
Overview
Descope is a modern customer identity platform designed for SaaS teams that need more flexibility than pre-built identity layers like Frontegg. It enables organizations to implement authentication, MFA, enterprise SSO, and authorization without being constrained by rigid components or opinionated abstractions.
Unlike Frontegg, which solely packages identity into embedded UI components and admin portals, Descope provides a cloud-native, developer-focused platform where authentication, authorization, and identity orchestration are managed through workflows, SDKs and APIs. This approach gives teams full control over user journeys while simplifying implementation and ongoing iteration. Descope also provides embeddable widgets and self-service identity delegation experiences, but for use cases where it makes sense rather than its sole offering.
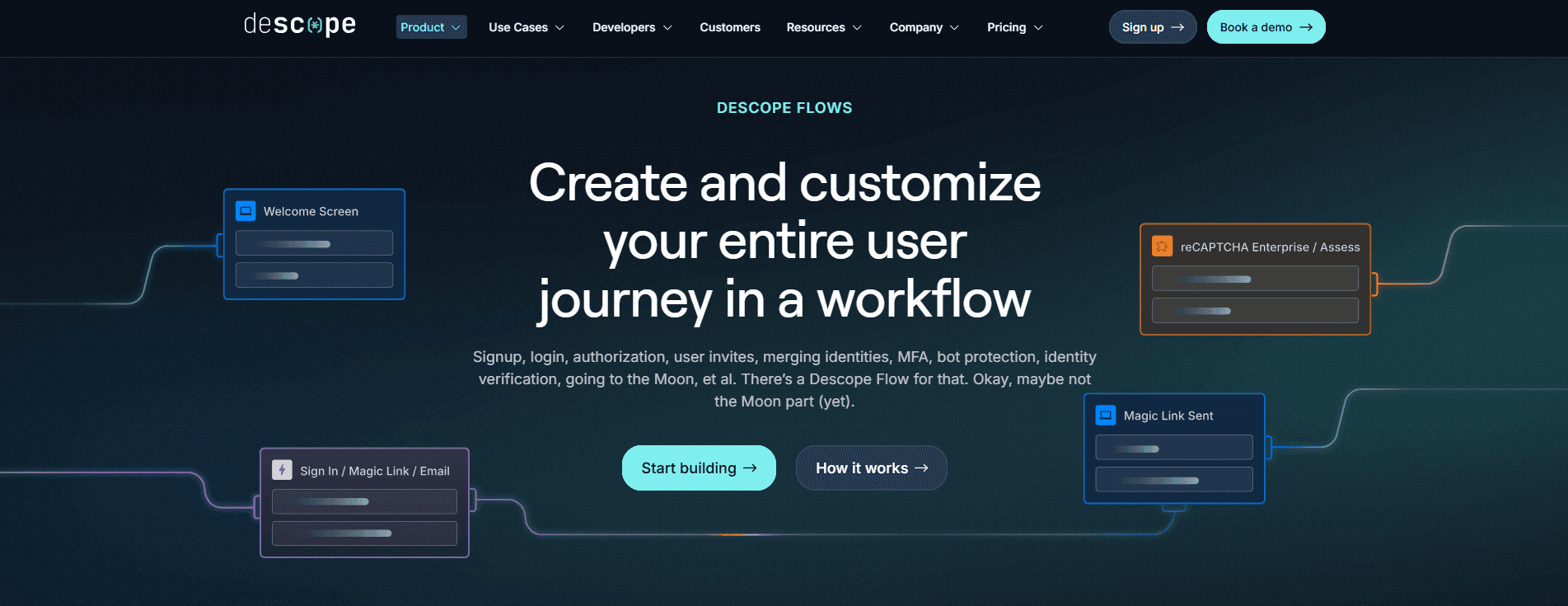
Descope is particularly well suited for B2B SaaS, B2B2C platforms, and applications that require complex multi-tenant identity, flexible onboarding, and seamless enterprise SSO. Its core differentiator is Descope Flows, a visual no-code / low-code orchestration layer that allows developers to design and modify login, MFA, SSO, onboarding, and step-up authentication journeys without rebuilding application logic. This enables faster iteration while maintaining centralized identity control.
Key capabilities
Advanced auth methods and security features
Support for passkeys, OTP, magic links, and social login for modern passwordless authentication experiences
Adaptive MFA, session protection, and bot detection using built-in and third-party risk signals, enabling dynamic step-up authentication within flows rather than as a separate system
Streamlined B2B and agentic identity
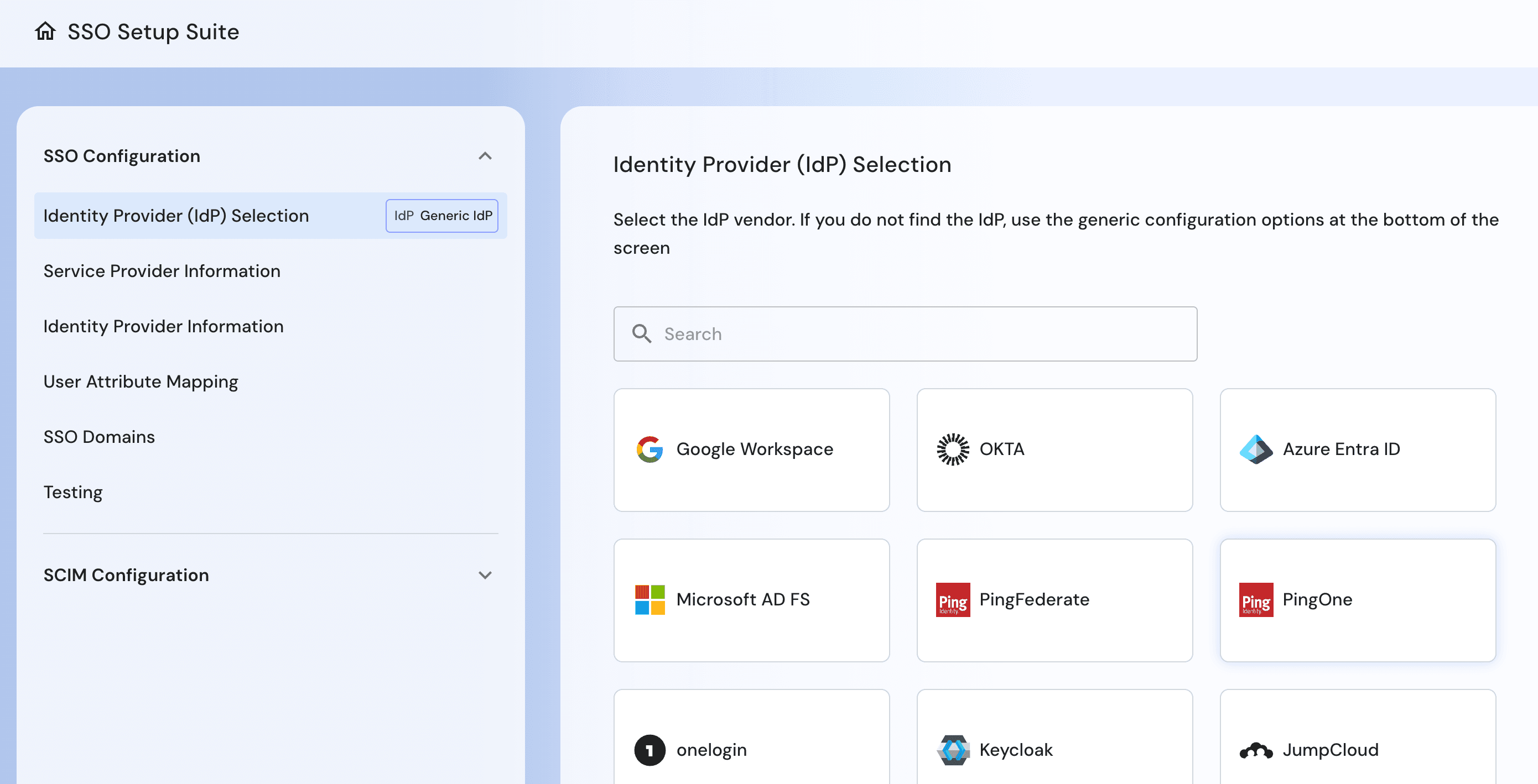
Self-service enterprise SSO with guided SAML, OIDC, and SCIM setup, reducing manual configuration and onboarding friction compared to more hands-on tenant provisioning approaches
Native multi-tenant identity with tenant-aware RBAC and FGA, designed for SaaS and B2B use cases without relying on rigid tenant models
Cloud-native identity orchestration across authentication, authorization, MFA, risk, and fraud signals within a single platform, avoiding the need to stitch together multiple layers of identity logic
Agentic identity support for AI agents and MCP-based ecosystems, extending authentication and authorization infrastructure beyond human users to secure AI systems.
Integration and connection support
Extensible integrations ecosystem for fraud detection, analytics, and identity enrichment within authentication workflows
Embeddable UI components for identity delegation, supporting both hosted and fully customized authentication experiences instead of limiting teams to predefined UI patterns
Powerful, flexible developer tooling
Visual workflow editor for login, signup, MFA, SSO, onboarding, and step-up authentication flows, allowing teams to modify user journeys without code changes instead of being constrained by pre-built components
15+ SDKs and APIs for web, mobile, and backend services, supporting modern API-first and microservices architectures
Strengths
Flexible identity orchestration instead of rigid components: Authentication logic can be customized through workflows rather than constrained by predefined UI and abstractions
Faster enterprise onboarding: Self-service SSO and SCIM reduce friction and eliminate manual configuration bottlenecks
Unified identity platform: Authentication, authorization, MFA, and risk signals are managed in one system instead of stitched together
Native multi-tenant architecture: Tenant-aware users, roles, and permissions are built in for SaaS and B2B environments
Adaptive and risk-based MFA built into flows: Dynamic authentication decisions can be enforced without additional tooling
Passwordless authentication out of the box: Passkeys, magic links, OTP, and social login are first-class capabilities
Reduced long-term complexity: Identity flows can evolve without re-architecting or rebuilding authentication logic
Built for modern SaaS architectures: Supports B2B, B2C, and hybrid use cases with flexible identity models
Broad SDK and API coverage: Integrates cleanly across applications and services without introducing bottlenecks
Ideal for
Descope is a strong choice for organizations evaluating Frontegg alternatives that want more flexibility and control over authentication and user journeys. It is well suited for teams that want to move beyond embedded, opinionated identity components and adopt a more configurable, workflow-driven approach.
It fits SaaS companies and digital product teams that require tenant-aware authentication, self-service enterprise SSO onboarding, adaptive MFA, and customizable identity flows that can evolve quickly without heavy engineering effort.
Descope is also ideal for B2B, B2C, and hybrid platforms that need unified authentication and authorization across customers, partners, administrators, and non-human identities within a single modern identity layer.
Auth0
Overview
Auth0, part of Okta, is a cloud-based customer identity platform frequently evaluated by teams looking for a more flexible and extensible alternative to platforms like Frontegg. While Frontegg emphasizes embedded components and B2B-focused abstractions, Auth0 provides a broader identity platform that supports both B2B and B2C use cases across a wide range of application architectures.
Auth0 delivers authentication, authorization, MFA, and federation as a managed service, with an API-first approach that allows developers to customize identity flows beyond predefined patterns. This makes it a common choice for teams that want greater control over authentication logic, deeper extensibility, and the ability to support diverse identity use cases as their applications evolve.
Key capabilities
Enterprise SSO with SAML, OIDC, and OAuth2 across a wide range of identity providers
Built-in MFA including WebAuthn, TOTP, SMS, email, and push
Extensible authentication logic using Actions and Rules for customizing user journeys
Hosted and embedded login experiences with support for branded and application-specific UX
Strengths
Flexible identity customization: Auth0 enables deeper control over authentication flows and logic compared to more opinionated, component-driven approaches
Broad identity coverage: Supports both B2B and B2C use cases within a single platform, rather than focusing primarily on embedded SaaS patterns
Cloud-native managed service: Eliminates the need to manage identity infrastructure while supporting scalable, modern application architectures
Extensible integration ecosystem: Prebuilt integrations and developer tooling allow teams to extend identity functionality without rebuilding core systems
Ideal for
Auth0 is well suited for organizations evaluating Frontegg alternatives that want greater flexibility and control over authentication and user journeys. It fits teams building applications that span B2B, B2C, or hybrid use cases and require extensible identity logic beyond predefined components.
Also Read: Why GoodRx Migrated Tens of Millions of Users From Auth0 to Descope
FusionAuth
Overview
FusionAuth is a developer-focused identity platform often evaluated by teams looking for greater control and cost predictability compared to platforms like Frontegg. While Frontegg emphasizes embedded UI components and managed SaaS delivery, FusionAuth provides flexible deployment options, including self-hosted and private cloud environments.
FusionAuth delivers authentication, authorization, and user management through APIs and SDKs, allowing teams to build and customize identity flows without being constrained by predefined abstractions. This makes it a strong option for organizations that want to own their identity infrastructure or avoid pricing models tied to feature usage and enterprise add-ons.
Key capabilities
Authentication, authorization, and user management APIs for full control over identity logic
Enterprise SSO with SAML, OIDC, and OAuth2 support
Flexible deployment options including self-hosted, private cloud, and managed cloud
Customizable authentication flows with full backend control
Strengths
Infrastructure control and flexibility: Teams can deploy FusionAuth in their own environment rather than relying on a fully managed SaaS model
Predictable pricing: Avoids feature-based pricing and scaling costs tied to enterprise capabilities like SSO
Customizable identity logic: Developers can fully control authentication flows without being limited by pre-built components
Broad protocol support: Supports standard identity protocols across enterprise and consumer use cases
Ideal for
FusionAuth is well suited for organizations evaluating Frontegg alternatives that want greater control over deployment, data, and pricing. It fits teams with strong engineering resources that prefer to manage identity infrastructure directly and customize authentication logic at a deeper level.
Amazon Cognito
Overview
Amazon Cognito is AWS’s native identity service, often evaluated by teams building within the AWS ecosystem as an alternative to platforms like Frontegg. While Frontegg provides embedded identity features and admin portals, Cognito offers a more infrastructure-aligned approach that integrates directly with AWS services.
Cognito provides authentication, user management, and federation capabilities, with customization handled through AWS-native tools like Lambda. This makes it a strong option for teams that want identity tightly coupled with their cloud infrastructure rather than layered through a separate identity platform.
Key capabilities
User pools for authentication, user management, and identity storage
Federation with SAML, OIDC, and social identity providers
Lambda triggers for customizing authentication workflows
Integration with AWS services such as API Gateway, IAM, and AppSync
Strengths
Deep AWS integration: Works seamlessly with AWS infrastructure and services, simplifying identity management for cloud-native applications
Scalable managed service: Handles authentication and user scaling without requiring infrastructure management
Flexible customization through Lambda: Developers can extend authentication flows using serverless functions
Broad federation support: Supports enterprise and social identity providers for diverse authentication scenarios
Ideal for
Amazon Cognito is well suited for organizations evaluating Frontegg alternatives that are already invested in AWS and want identity integrated into their existing cloud stack. It fits teams that prefer infrastructure-native services over standalone identity platforms.
Keycloak
Overview
Keycloak is an open-source identity and access management platform often considered by teams looking for a self-hosted alternative to platforms like Frontegg. While Frontegg provides a managed, embedded identity layer, Keycloak offers full control over identity infrastructure and configuration.
Keycloak supports authentication, SSO, and federation across a wide range of protocols, with customization handled through configuration and extensions. This makes it a strong option for organizations that prioritize flexibility and control over convenience and managed services.
Key capabilities
Support for SAML, OAuth2, and OpenID Connect authentication
Built-in single sign-on and identity federation
User federation with LDAP and Active Directory
Admin console and user self-service account management
Strengths
Open-source flexibility: Provides full control over identity infrastructure without vendor lock-in
Strong enterprise protocol support: Supports standard identity integrations across enterprise environments
Extensible architecture: Allows customization through plugins and service provider interfaces
Self-hosted deployment: Enables organizations to manage identity within their own environment
Ideal for
Keycloak is well suited for organizations evaluating Frontegg alternatives that want full control over their identity stack. It fits teams with the operational resources to manage and maintain a self-hosted identity platform.
Ory
Overview
Ory is a modular, API-first identity platform often evaluated by teams that need maximum flexibility compared to platforms like Frontegg. While Frontegg packages identity into higher-level abstractions, Ory provides low-level building blocks for authentication, OAuth2, and authorization.
Ory is composed of services such as Kratos for authentication and Hydra for OAuth2, allowing teams to design identity systems tailored to their architecture. This approach is well suited for microservices and API-first environments where identity needs to be deeply integrated into application logic.
Key capabilities
API-driven authentication with Ory Kratos
OAuth2 and OpenID Connect server through Ory Hydra
Fine-grained authorization through modular services
Self-hosted and managed deployment options
Strengths
Composable architecture: Identity services can be deployed and combined based on specific application needs
API-first design: Enables deep integration with microservices and backend systems
Open-source flexibility: Provides full control over customization and infrastructure
Designed for modern architectures: Well suited for distributed systems and API-driven applications
Ideal for
Ory is well suited for organizations evaluating Frontegg alternatives that want full flexibility and are comfortable building identity systems from modular components. It fits engineering teams that prioritize customization and control over out-of-the-box functionality.
Also Read: Why BalkanID Moved From Ory Kratos to Descope
Conclusion
Frontegg is a strong starting point for SaaS teams that want to quickly add authentication, user management, and enterprise features like SSO and multi-tenancy. However, as applications scale, its opinionated approach can limit flexibility, customization, and long-term scalability.
Modern applications require customizable authentication flows, seamless enterprise onboarding, and deeper control over identity logic. In these environments, predefined components can introduce friction and slow iteration.
Among the alternatives, Descope stands out for teams that want a flexible, workflow-driven identity platform that unifies authentication, authorization, enterprise SSO, and adaptive MFA. By replacing rigid components with configurable workflows and APIs, Descope helps teams scale identity without added complexity.
If you're evaluating Frontegg alternatives, and you'd like a demo, meet with our auth experts. Also, if you want to try Descope yourself, sign up for a Free Forever Account and start dragging & dropping your auth today!