Table of Contents
TL;DR
Hello Descopers! Today, we’re excited to share our first major pricing update since we introduced the Growth tier over a year ago. This update formalizes pricing units for the Descope Agentic Identity Hub and moves to a more common-sense approach for machine-to-machine (M2M) authentication pricing while ensuring customers continue getting more value from their Descope plan.
We realize agentic identity is an emerging space that’s evolving quickly. These pricing updates have been made in collaboration with our developer community with the following goals in mind:
M2M and agentic identity essentials should be available to all developers on all plans, including the Free Forever tier.
Fees should be focused on differentiated Descope features or processes that involve real operational cost.
You can view our pricing details here. If you’re a customer and have questions after going through this blog, please reach out to your Descope account representative or contact us.
TL;DR
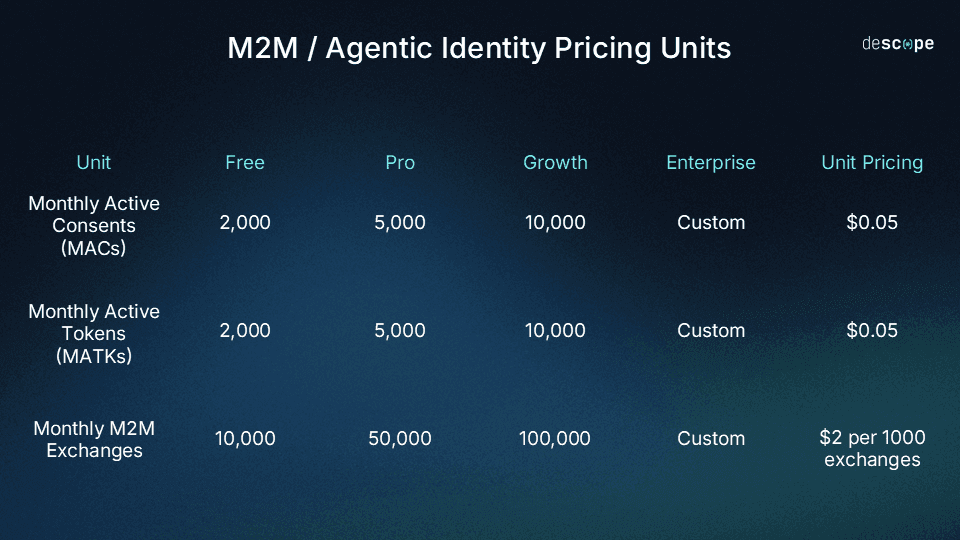
Here is a summary of our M2M and agentic identity pricing updates:
Monthly Active Consent (MAC): Any instance when a unique user consents to any scope for a specific resource at least once in a month. Relevant to scenarios where Descope Inbound Apps or MCP authentication are used.
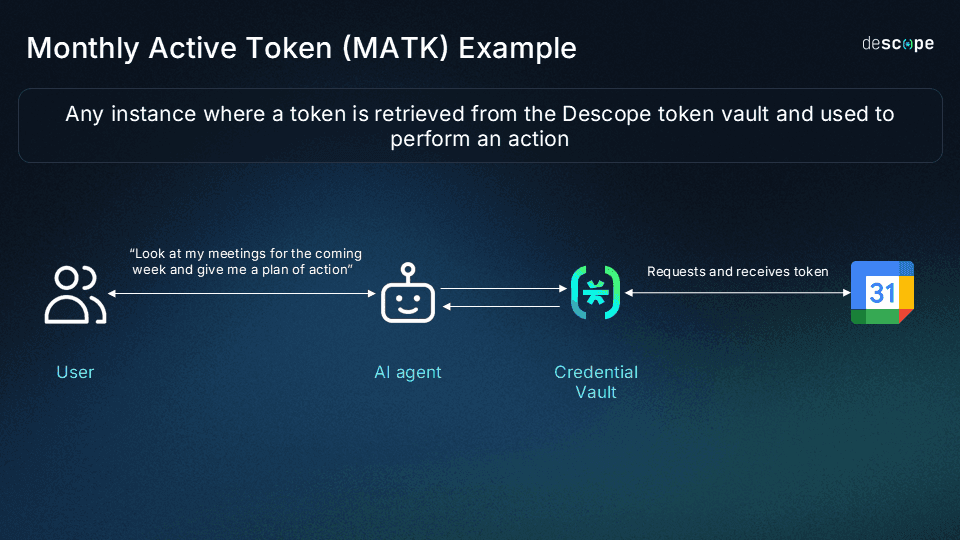
Monthly Active Tokens (MATK): Any instance where a token is fetched and used to perform an action. Relevant to scenarios where Descope Outbound Apps or Connections are used.
M2M Exchanges: Any token exchange using machine-to-machine flows (such as client credentials, OAuth token exchange, or access key exchanges). Relevant to any scenario (M2M auth or agentic identity) where a token is exchanged for another token with different audience and scopes.
Here’s a summarized look at what’s included in each tier along with per unit pricing.
Let’s dive into the specifics.
Monthly Active Consents (MACs)
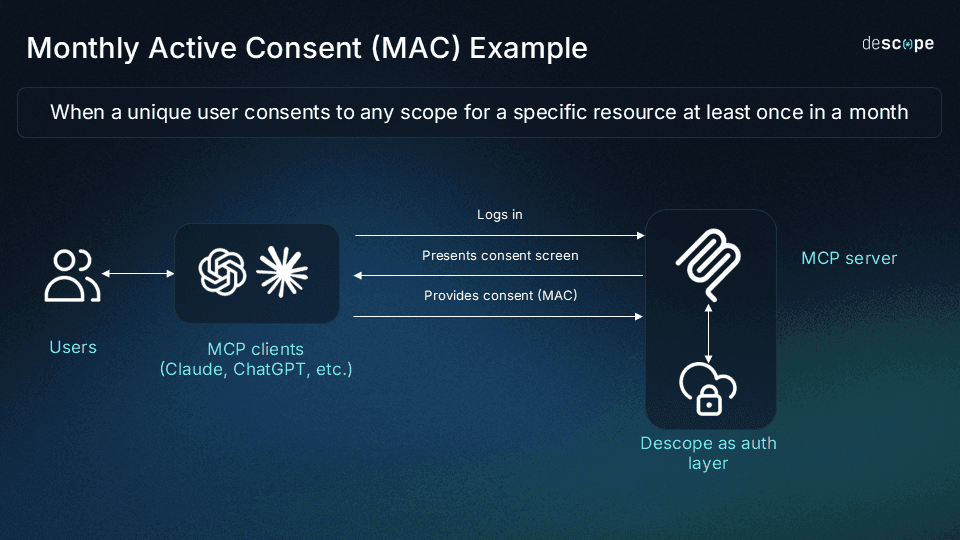
A Monthly Active Consent (MAC) is counted when a unique user consents to any scope for a specific resource at least once in a month. This resource can be an MCP server or your product APIs that have been protected by OAuth using Descope Inbound Apps.
MAC example: MCP auth
Let’s say you are an AI data analytics startup that helps customers derive business insights from structured and unstructured data. You build a customer-facing MCP server protected by Descope that lets your customers connect to your product using Claude, ask questions like “How many customers do I have in my pipeline and what’s preventing them from closing this quarter?”, and get answers from your product directly in their LLM chat interface.
When an end user connects to your MCP server, they will log in and be shown a consent screen that shares what scopes the MCP client is requesting on their behalf (e.g. “read contact records”, “read deal records”). These scopes will be granted to the MCP client only after the user authorizes–that’s a MAC.
MAC example: Inbound Apps
Let’s say your app, HighFinance, helps users invest in curated high-growth stocks. Another popular app among your user base is WealthCentral, an app to centralize and view their entire investment portfolio.
Using Inbound Apps, users can grant consent to WealthCentral to access and display their investment data from HighFinance, increasing the value that both apps provide to users while ensuring secure API connections.
When an end user clicks a button on WealthCentral to initiate this process, they will be shown a consent screen that shares what scopes WealthCentral is requesting on their behalf (e.g. “read account summary”). This scope will be granted to WealthCentral only after the user authorizes–that’s a MAC.
A few pointers to keep in mind:
If the same user consents to the same scopes for the same resource multiple times within a month, your MAC count stays the same.
If the same user consents to the same scopes for two different resources within a month (e.g. two MCP servers), your MAC count increases.
If the same user consents to the same resource but the scopes are different (e.g. “write contact records”), your MAC count increases.
Monthly Active Tokens (MATKs)
A Monthly Active Token (MATK) is any instance where a token is retrieved and used to perform an action. This token can be for a downstream connection from your app using Descope Outbound Apps, or a downstream connection from your AI agent using Connections.
MATK example: AI agents
Let’s say you’ve built a productivity AI agent that summarizes users’ schedules by looking at their Google Calendar and uses Descope as its credential vault. If a user asks the agent: “Look at my meetings for the coming week and give me a plan of action”, the agent will request scopes for reading the user’s Google Calendar (with Descope acting as the token management service) and fulfill the request. That’s an MATK.
MATK example: Social connections
Let’s say you have an app to let users create booklists and rate the books they have read that uses Descope for customer auth. You add a “share on Facebook” option powered by Descope Outbound Apps that lets users share what book they’re reading on Facebook directly from your app.
If a user clicks this button, your app will request scopes for posting on Facebook on the user’s behalf (with Descope acting as the token management service) and fulfill the request. That’s an MATK.
A few pointers to keep in mind:
An MATK is only counted for downstream / third-party connections where Descope is the credential vault. If your AI agent is accessing your app’s backend APIs, for example, that’s not counted as an MATK.
If the same user / AI agent connects to the same downstream service with the same scopes multiple times per month, your MATK count stays the same.
An MATK is only counted when it’s active–you don’t pay for storage, you only pay when a token is retrieved and used from Descope’s vault. In the bookreading app example from earlier, if you have a Facebook token for a user but they never click the “share on Facebook” button in a month, it’s not counted as an MATK.
If it’s the same user and the same app but the scopes requested are different, your MATK count will increase (e.g. scopes to read Google Calendar and write to Google Calendar).
If the same user connects to the same app using two different user handles, your MATK count will increase. For example, a user connecting two of their Facebook profiles from the bookreading app would count as two MATKs when the tokens are retrieved.
M2M Exchanges
An M2M exchange is any token exchange using machine-to-machine flows. A simple way to think about when something is an M2M exchange:
Whenever you exchange a token you already have for another token with a new audience or different scopes (e.g client credentials flow, OAuth token exchange, exchanging an access key for a JWT).
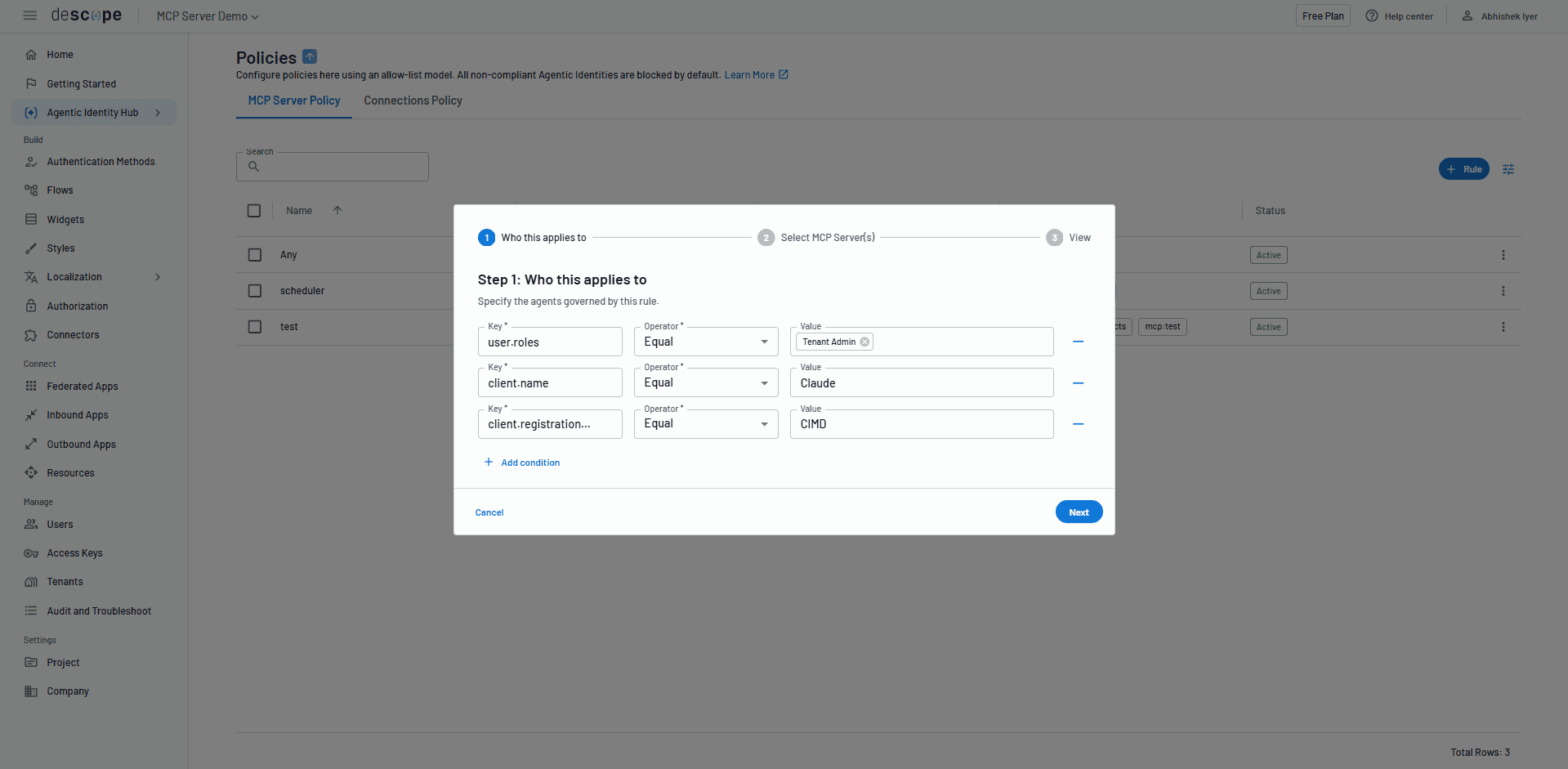
Whenever Descope Policies are enforced for MCP servers or AI agents.
These exchanges are billable because they enable secure delegation between services and agents and / or involve policy enforcement.
M2M exchange example: Access keys
Let’s say you have a B2B SaaS app that uses Descope for customer and M2M auth. You use Access Key Management Widgets to let your customer admins create access keys that let other machines access your app. Whenever a machine presents their access key and gets a JWT in return, that’s an M2M exchange.
M2M exchange example: MCP policy control
Let’s consider the same MCP example as the one mentioned earlier in this blog (the data analytics startup with a customer-facing MCP server). However, you now don’t just want the MCP server protected by auth and consent, but you also want to apply a policy that allows only Claude agents that register through CIMD on behalf of users with an Admin role.
When an end user connects to your MCP server in this context, the policy will be enforced and this will be both a MAC and an M2M exchange.
M2M exchange example: AI agent downstream connections
Consider the same productivity AI agent example from the MATK section. If a user asks the agent: “Look at my meetings for the coming week and give me a plan of action”, the agent will request scopes for reading the user’s Google Calendar (with Descope acting as the token management service) and fulfill the request.
This is an MATK (as we covered earlier). But it’s also an M2M exchange, since a possessed token is exchanged for another token with different audiences / scopes.
A few pointers to note:
Every MATK interaction (e.g. an AI agent accessing a downstream service to perform an action on the user’s behalf) is also an M2M exchange.
While an MATK is only counted for downstream / third-party connections, an M2M exchange is counted for all connections. For example, if your AI agent is accessing your app’s backend APIs, it doesn’t count as an MATK but it does count as an M2M exchange.
Secure machine identity for everyone
Our goal is to continue being a customer and agentic identity platform that’s loved by developers and security teams alike. If you’re a current customer reading this, thank you for using Descope as your trusted authentication provider. If you’re not a customer, we hope this pricing update is clear and transparent enough for you to give Descope Agentic Identity Hub and M2M auth a try.
You can review our pricing here and reach out to us with any questions or comments. Thanks for reading!