Table of Contents
What is an authentication server?
A key aspect of maintaining and implementing authentication is the use of authentication servers. Authentication servers are servers that are specifically used to verify a person's identity when they need to prove who they are to a server or application.
In this post, we’ll explore the importance of these servers in authentication, as well as how they work under the hood.
What is an authentication server?
Authentication is the process of validating if a user that’s logging in to a website or application is who they say they are. Therefore, an authentication server is just the server that handles that validation. These servers act as barriers between an app server and client, to ensure that only users with proven identities can obtain access to sensitive information.
Although authentication doesn’t necessarily require the use of dedicated servers, they can provide a more efficient and secure method of managing access to a website or application.
How does an authentication server work?
The typical process for how an authentication server works is straightforward if you’re somewhat familiar with how the normal authentication process works. Most authentication servers nowadays use the OAuth 2.0 protocol.
Starting out, a user who wants to access a protected application, makes a request to that application which points them to the authentication server.
That authentication server will grant access, assuming that it can successfully verify the user’s identity, and then return an access token.
That access token can then be used by the user and application to access a resource server and fetch all of the protected information that it needs.
Authentication protocols at play
Authentication servers function by comparing the credentials provided by a user (such as a username and password, or a digital certificate) with information stored in the server. This information may be held on the authentication server itself or on a separate database.
If the submitted credentials match the stored information, the server grants access to the requested resource. The way this is done depends on how the authentication is implemented (either cookie or token-based).
There are a variety of authentication protocols that authentication servers use to validate the credentials of users requesting access, including but not limited to:
Password Authentication Protocol (PAP): A simple password-based authentication protocol where an unencrypted password and user information are sent and received between a client and a server. Although common, this is considered one of the most vulnerable authentication protocols, mostly due to the lack of encryption.
Challenge-Handshake Authentication Protocol (CHAP): This method utilizes a challenge-response system with a “secret”. The server “challenges” the client to produce the correct response from an MD5 hash function. If the client cannot give the correct response, the connection request is denied. This required encrypted “handshake” between client and server makes CHAP a far more secure protocol than PAP.
Extensible Authentication Protocol (EAP): This framework is one that supports multiple types of authentication methods, including: OTPs, certificates, and biometric authentication. In EAP, a user requests connection to a wireless network through an AP – a station that transmits and receives data. That AP then requests identification data from the user and transmits that data to an authentication server. Once the authentication server confirms that the information is valid, the user is authenticated.
Lightweight Directory Access Protocol (LDAP): This directory-based service protocol is used to access and manage information stored in a hierarchical directory structure. Although used primarily in enterprise-level applications, services such as Kerberos use symmetric key cryptography and LDAP to authenticate and verify user identities.
In most cases, the information stored server-side will either be information about the user’s session or a public key that is used to verify the signature of a privately-signed JWT. The former is also known as stateful authentication, while the latter is known as stateless authentication.
In practice, stateless authentication is usually preferred as it does not require the server to store user session information. Rather, a singular public RSA key is used to validate the signature of many different JWTs that are sent out from the server.
Here's a simple comparison of stateless and stateful approaches:
Stateless | Stateful |
|---|---|
Does not require the server to retain information about the session. | Requires a server to save information about a session. |
Server design and architecture is simple. | Server design and architecture is relatively complex. |
Handles crashes well since servers are treated as cheap commodity machines. | Does not handle crashes well since servers are treated as valuable and long-living. |
Easier to scale. | Tougher to scale. |
By combining the stateless nature of JWTs, with a secure authentication protocol like EAP, authentication servers can easily ensure that all application users are identified efficiently and securely.
The importance of authentication servers
Authentication servers play a crucial role in ensuring digital security. By managing the authentication process in a centralized manner, they offer several key advantages to developers:
Scalability: More users of any platform mean more people requiring access to that platform, which in turn means more authentication requests. Authentication servers allow you to easily scale with this growth, allowing the server to identify more users quickly and efficiently.
Simplified management: If the authentication process and all associated information is centralized, it’s easier for system administrators to manage user access, enforce security policies, and monitor activity across the entire platform.
Single Sign-On (SSO): With the use of authentication servers, servers can enable SSO for specific users, allowing them to access multiple services with a single set of credentials and thus streamlining the login process.
As digital security continues to be a crucial part of all web development, it’s important to understand how these authentication servers work and the importance they hold in the broader authentication process. The next step that usually follows, once a user has been authenticated, is to verify that a user can see the protected resource they are trying to access. This is called authorization.
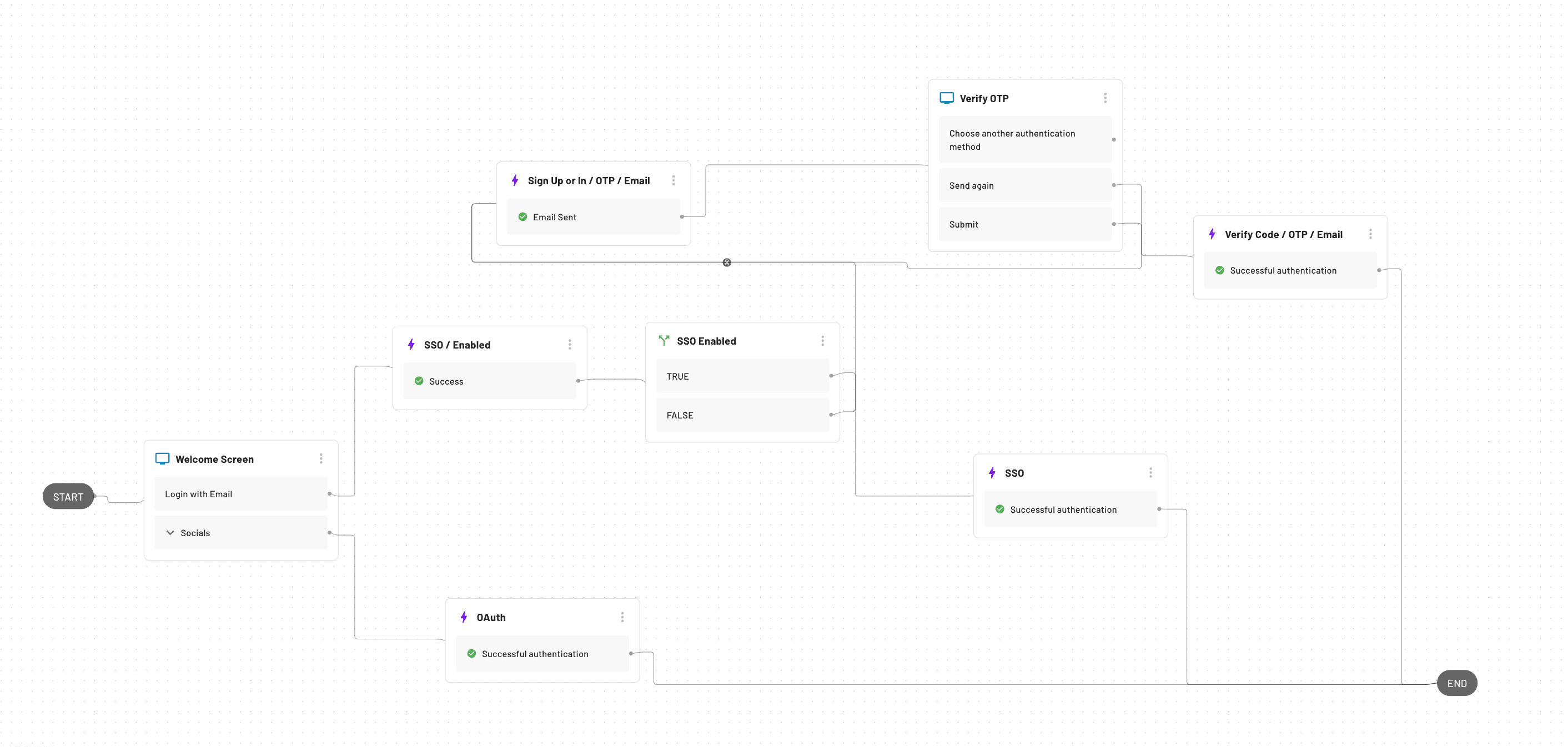
To better understand how a typical authentication process works, sign up for Descope and open up a drag-and-drop workflow to help visualize the process from start to finish.