Table of Contents
Why developers seek Stytch alternatives
Stytch is a modern authentication platform that many developers explore when adding passwordless login, MFA, and user management to their applications. Its clean APIs, polished documentation, and elegant UX make it appealing for teams that want a quick, low-friction way to launch authentication.
However, as products grow, developers often discover that Stytch’s focus on auth building blocks increases the amount of custom engineering required. Because teams must assemble and maintain the auth logic themselves, adding new requirements becomes time-consuming. As orgs introduce more complex user journeys, they encounter additional overhead costs and slowed development.
Below, we break down the top reasons developers look beyond Stytch, then compare eight top Stytch alternatives based on security, extensibility, multi-tenancy, and long-term maintainability.
This guide will cover:
Why dev teams outgrow Stytch
An overview of the top 8 Stytch alternatives
A deep dive into each contender’s strengths and fit
A practical guide to finding the right Stytch alternative
Why developers seek Stytch alternatives
Stytch is a great starter solution for quickly getting auth flows into an app. However, it’s not always ideal for scaling, so dev teams often outgrow it.
On a macro-level, Stytch lacks support for robust security features within auth:
Authorization: Stytch provides basic tenant-scoped RBAC but lacks attribute-based authorization, contextual/risk-driven policies, admin tooling, or lifecycle automation.
MFA limitations: Not all authentication methods can be used as MFA. Adaptive or risk-based MFA is not available. Passkeys and magic links cannot be used as MFA methods.
Fragmented identity model: Stytch treats B2C and B2B as separate products, creating different workflows and patterns to manage rather than a single unified identity platform.
Orchestration gaps: Stytch offers little built-in support for user lifecycle workflows, enrichment, or business logic automation, which creates more work for dev teams.
On a micro-level, Stytch has security limitations with respect to session management:
Session revocation: Stytch provides session revocation APIs, but global logout typically requires identifying and revoking sessions individually, adding implementation complexity for multi-device scenarios.
Session constraints: Abstracted session and token handling limit long-lived sessions, service tokens, and fine-grained lifecycle control, further complicating support.
There are also issues with respect to multi-tenant management with Stytch:
Lack of support for multi-tenancy: Stytch offers basic multi-tenant objects but leaves all orchestration to engineers, which can lead to bottlenecks when projects scale.
Role limits per tenant: Some teams encounter limits, as low as 10, on custom roles per tenant, restricting granular permission modeling without engineering workarounds.
Weak tenant and B2B support: Stytch’s B2B offering is relatively new and lacks native FGA, enterprise IdPs, and advanced federation that streamline auth in B2B use cases.
Integration can also become a pain point with Stytch:
Limited integration capabilities: Stytch’s Connected Apps let you act as an OAuth or OIDC identity provider, but they do not support data-level integrations with external services, leaving these integrations to custom engineering and more complex dev workloads.
Rigid integrations where available: Integrating with legacy systems or migrating from an existing identity provider often requires re-architecting authentication flows.
Finally, some teams find that Stytch becomes harder to manage as requirements and user complexity grow:
Limited flexibility and high engineering effort – Stytch’s building blocks require teams to maintain complex auth flows, slowing updates as requirements change.
Cost unpredictability – Pricing can scale quickly as MAU, MFA usage, or advanced features grow. What starts as an inexpensive solution may not be for long.
Each alternative below addresses these gaps differently depending on your technical requirements, ecosystem, and growth stage.
Stytch alternatives at a glance
Here’s how the top 8 Stytch alternatives stack up:
| Features | Strengths | Best for |
|---|---|---|---|
Descope | • Adaptive MFA • Multi-tenancy • Workflow orchestration • Connectors • Developer tooling | • Unified B2C/B2B identity • Workflow-based auth • Tenant-aware SSO • Fine-grained authorization • Support for AI agents and MCP | Teams seeking robust auth features without additional complexity |
Auth0 | • Enterprise SSO • MFA options authorization • Customizable UIs | • Broad protocol support; flexibility • Established integrations/connections | Enterprise-level teams seeking broad standards support and SSO |
Cognito | • Managed user pools • Federation • MFA • Easy AWS integration | • Fully managed service • Reliable performance • Security alignment | Teams invested in AWS architecture seeking backend integration |
Firebase | • Multiple auth methods • Varied SDKs • Seamless Google integration | • Swift setup • Mobile-friendly • Integrated backend | Early-stage teams seeking simple auth tied to a managed backend |
Supabase | • Passwordless auth • Row-level security • Serverless edge options • SDK compatibility | • Unified backend • Postgres Row-level security • Flexibility | Teams building data-intensive apps seeking unified tooling |
Keycloak | • SSO via OIDC, OAuth, SAML • ID brokering • Built-in admin console | • Open-source flexibility • Enterprise compatibility • Strong extensibility | Teams seeking open-source auth with SSO and federation |
Ory Kratos | • API-driven customization • Self- or cloud-hosting • FGA | • Modular auth options • Flexibility • Strong open-source base | Teams seeking maximum control and customization |
FusionAuth | • OAuth, OIDC, SAML support • Advanced MFA • Multi-tenant functions | • Enterprise features • Flexibility • Wide coverage for SSO protocols | Teams seeking powerful auth and self-hosting or cloud deployment |
Below, we’ll look more closely at what makes each one unique.
Descope
Overview
Descope is a modern customer and agentic IAM platform built for developers who want flexible, secure authentication without taking on the overhead of managing complex infrastructure.
Unlike Stytch, which separates B2C and B2B capabilities into different products and places constraints on customization, Descope provides a unified multi-tenant platform focused on simplicity, speed, and full control of identity flows for customers, partners, AI agents, and MCP servers.
Descope is particularly strong for B2C and B2B SaaS applications that need tenant-aware SSO, fine-grained authorization, and rich orchestration. It also supports new identity frontiers such as AI agents and MCP-based ecosystems where delegated trust and secure automation are essential.
Descope’s unique approach is based on Descope Flows, a no / low code journey-time orchestration interface that lets teams visually design flows for authentication, MFA, SSO, consent management, AI agent authentication, and more.
Customer Story: Why You.com Moved From Stytch to Descope
Key capabilities
Advanced auth methods and security features
Auth support via passkeys, OTP, magic links, social login, and Google One Tap.
Advanced protections like Adaptive MFA, session protection, and bot detection.
Streamlined B2B/enterprise environments
Identity orchestration coordinates authentication, authorization, and fraud tools.
Agentic identity support to get agents enterprise-ready and orgs agent-ready.
Integration and connection support
Plug & play connectors ecosystem with 50+ third-party tools
Anonymous user tracking for top-of-funnel B2C user visibility
Embeddable UI widgets for self-service profile and admin management.
Powerful, flexible developer tooling
Visual workflow editor to create and modify login, signup, and MFA flows
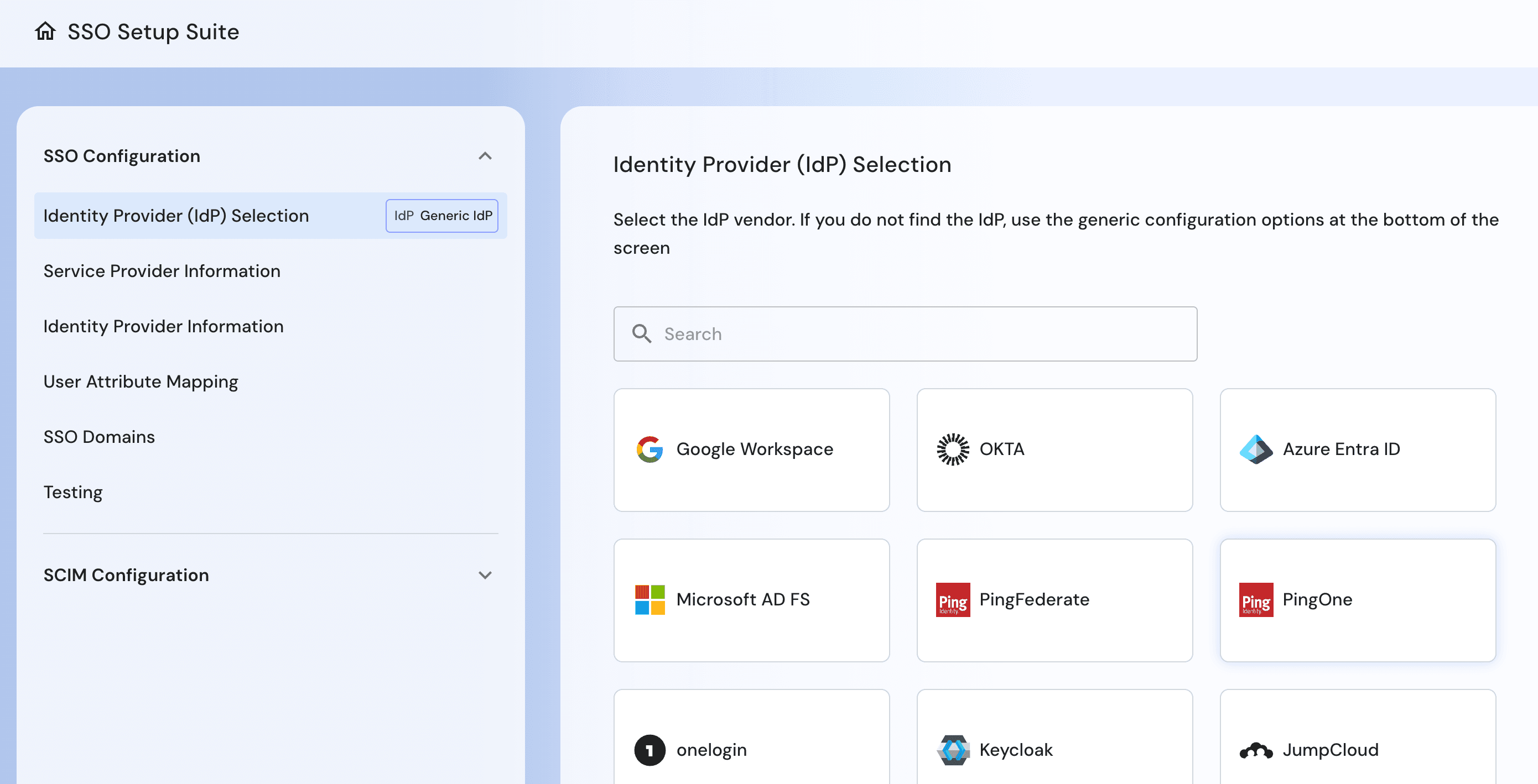
SSO Setup Suite to enable end-to-end SSO and SCIM setup, mapping, and testing
15+ SDKs and APIs spanning web, mobile, and a robust REST API.
Strengths
Visual workflows: Descope’s drag & drop editor lets developers design login, signup, MFA, and SSO flows without backend scripting or custom glue code. This simplifies auth implementation and speeds up time to production.
Predictable pricing and responsive support: Descope offers transparent, usage-based pricing with no hidden fees or surprise jumps. Teams benefit from fast, knowledgeable support to help them implement, troubleshoot, and scale with confidence, as evidenced by Descope winning the Best Support G2 badge the last five quarters in a row.
Streamlined SSO: Build and manage SSO journeys with workflows, enable self-service setup, and migrate existing configurations with no disruption.
Passwordless authentication: Descope supports passkeys, magic links, OTP, and social login natively. These methods can be easily added to any flow, reducing reliance on passwords while improving UX and security.
Omnichannel authentication: With Descope, authentication flows can be unified across web, mobile, and third-party or partner applications. The same no-code or low-code workflows can be reused across environments, making updates and scaling easier over time.
Adaptive MFA: Descope allows developers to choose from a wide range of MFA methods and integrate seamlessly into their flows. MFA can be enforced only when needed using native and third-party risk signals, without overhauling existing auth systems.
AI agent ready: Descope supports secure authentication and access control for AI agents and MCP servers with its Agentic Identity Hub.
Built for developers: Whether using hosted components or fully custom UIs, Descope gives developers flexibility with SDKs and APIs in React, Node.js, Python, Flutter, and more. The platform fits into any tech stack without locking teams into rigid patterns.
Also Read: Complete Descope vs Stytch Comparison
Ideal for
Descope is a strong choice for developers and product teams that want to launch and scale authentication without taking on the operational complexity that often appears when using Stytch for multi-tenant, enterprise, or orchestration-heavy environments. It is also well suited for AI-driven applications that require identity controls for both users and autonomous agents.
Descope is particularly apt for B2B SaaS, multi-tenant apps, projects that need to balance security and UX across both customer and partner identities, and AI-native products.
Customer Story: Why Branch Insurance Chose Descope Over Stytch
Auth0
Overview
Auth0, part of Okta, is an established external identity platform and has been a popular choice for teams that want a mature, enterprise-ready solution. While Stytch focuses on clean developer UX and passwordless-first design, Auth0 offers a broader feature set with extensive protocol support, advanced SSO capabilities, and a long track record in large-scale deployments.
For teams that need maturity and broad standards coverage, Auth0 remains a leading alternative to Stytch, especially for applications that must integrate with a wide range of enterprise identity providers.
Key capabilities
SAML, OIDC, and OAuth2 support for enterprise-grade SSO
MFA options including WebAuthn, TOTP, SMS, and push notifications
Rules and Actions for extending authentication and authorization logic
Hosted login pages and customizable UIs for user journeys
Strengths
Broad protocol support: Works with SAML, OIDC, and OAuth2 for common enterprise SSO needs.
Flexible extensibility: Rules and Actions allow customization of authentication and authorization flows.
Established integrations: Offers a wide range of prebuilt connections to identity, analytics, and developer tools.
Ideal for
Auth0 is well suited for organizations that need a mature, enterprise-ready identity platform with broad standards support. Companies evaluating Stytch and looking for more extensive SSO capabilities often consider Auth0 when enterprise identity compatibility and protocol coverage take priority.
Also Read: Why GoodRx Moved From Auth0 to Descope
Amazon Cognito
Overview
Amazon Cognito is AWS’s fully managed authentication and user management service. It integrates directly with the AWS ecosystem and handles scaling, infrastructure, and availability without additional operational overhead.
Compared to Stytch, Cognito offers stronger native ties to backend services and is often selected by teams that want to consolidate identity and infrastructure within AWS.
Key capabilities
Managed user pools for authentication and user management
Federation with social and enterprise identity providers
MFA and adaptive authentication options
Integration with API Gateway, Lambda, and AWS IAM
Strengths
Fully managed service: Reduces operational work by handling scaling, availability, and updates.
AWS integration: Connects directly to AWS services for API security, access control, and backend workflows.
Reliable performance: Designed to support high-volume applications without custom scaling logic.
Security alignment: Benefits from AWS compliance standards and defaults.
Ideal for
Teams already invested in AWS infrastructure that want a managed identity service with strong backend integrations. Cognito is a strong Stytch alternative for applications that need deep ties into AWS services or long-term operational stability.
Firebase Authentication
Overview
Firebase Authentication is Google’s developer-focused identity service designed for fast, simple onboarding across mobile and web applications. Many teams start with Firebase because it offers quick setup, client-side SDKs, and seamless integration with Firestore, Cloud Functions, and other Firebase tools.
Compared to Stytch, Firebase provides a more unified backend experience but offers less flexibility for multi-tenant or enterprise scenarios. It is well suited for projects that prioritize rapid development, mobile-first workflows, and minimal authentication infrastructure.
Key capabilities
Email and password authentication, OTP, and magic links
Social login with major identity providers
SDKs for iOS, Android, and web frameworks
Seamless integration with Firestore, Storage, and Cloud Functions
Strengths
Fast setup: Developers can enable common login methods in minutes with minimal configuration.
Mobile-friendly SDKs: Strong support for Android, iOS, and cross-platform frameworks.
Integrated backend: Works directly with Firestore and other Firebase products for simplified data and auth workflows.
Ideal for
Early-stage products, mobile apps, and teams that want a simple authentication layer tied closely to a managed backend.
Supabase
Overview
Supabase Authentication is built on GoTrue and tightly integrated with Supabase’s Postgres database, storage, and serverless functions. It appeals to teams that want an open-source backend with authentication built directly into the data layer.
Compared to Stytch, Supabase offers a more unified developer experience but provides fewer enterprise features for multi-tenancy, SSO, and advanced orchestration. It is a strong choice for applications that rely heavily on Postgres and want authentication, authorization, and database logic to work together without managing separate services.
Key capabilities
Email and password authentication, magic links, and OAuth providers
Postgres row-level security for fine-grained access control
Serverless Edge Functions for custom backend logic
Self-hosted or fully managed deployment options
SDKs for JavaScript, Flutter, and other platforms
Strengths
Unified backend: Authentication, database, and functions work together without extra wiring.
Row-level security: Ties authorization directly to Postgres, reducing custom logic.
Flexible deployment: Supports both managed hosting and self-hosted setups.
Ideal for
Developers building data-intensive applications on Postgres who want integrated authentication and backend services. Supabase is a practical Stytch alternative for teams prioritizing unified tooling and open-source flexibility.
Keycloak
Overview
Keycloak is a widely adopted open-source identity and access management platform maintained by Red Hat. It provides built-in SSO, identity brokering, user federation, and an admin console, which gives teams more enterprise capabilities than Stytch offers out of the box.
While Keycloak requires more operational work and infrastructure management, it is valued for its extensibility, open-source control, and ability to handle complex federation and policy requirements. It is a strong fit for teams that want full ownership of their identity stack and need features that go beyond Stytch’s primarily developer-focused, API-driven model.
Key capabilities
SSO support for OIDC, OAuth2, and SAML
Identity brokering and social login integration
LDAP and Active Directory federation
Built-in admin console and user self-service portal
Strengths
Open-source flexibility: Provides full control for teams that want to customize and self-host.
Enterprise compatibility: Integrates well with legacy identity systems and on-premise environments.
Extensible architecture: Supports plugins and SPI for deeper customization.
Active community: Benefits from broad community adoption and regular contributions.
Ideal for
Organizations that want an open-source identity system with strong SSO and federation capabilities. Keycloak is a suitable Stytch alternative for teams willing to manage infrastructure in exchange for greater control and customization.
Ory Kratos
Overview
Ory is an open-source, API-first identity suite built from modular components such as Ory Kratos, Ory Hydra, and Ory Keto. It offers extensive flexibility for teams that want to assemble a custom identity architecture rather than rely on a single managed platform.
Compared to Stytch, Ory provides significantly more control over authentication, authorization, and policy logic but requires more engineering effort and operational ownership. It is a strong option for teams that need fine-grained control, self-hosting, or distributed identity workflows that exceed the constraints of Stytch’s more opinionated approach.
Key capabilities
Modular components for identity, OAuth2, and authorization
Self-hosted or cloud-managed deployment options
API-driven approach for full customization
Policy engine for fine-grained access control
Strengths
Modular design: Allows teams to adopt only the identity components they need.
High flexibility: Supports custom authentication and authorization patterns.
Self-hosting options: Enables full control over infrastructure, data, and compliance.
Strong open-source base: Backed by an active community and transparent development.
Ideal for
Engineering teams that want to build a custom identity system with complete control over each component. Ory is a suitable Stytch alternative for applications that require advanced policy models, self-hosting, or a modular approach to authentication and authorization.
Also Read: Why BalkanID Moved From Ory Kratos to Descope
FusionAuth
Overview
FusionAuth is a full-featured customer identity platform that can be deployed as a managed cloud service or fully self-hosted. It provides a comprehensive set of authentication and authorization features, including multi-tenancy, WebAuthn MFA, and an event-driven extension model.
Compared to Stytch, FusionAuth offers stronger enterprise capabilities and more configuration options, although it requires a greater investment in setup and ongoing management. It is a strong option for teams that want flexibility, advanced policy controls, and the ability to run identity infrastructure on their own terms.
Key capabilities
Support for OAuth2, OIDC, and SAML-based SSO
WebAuthn, TOTP, SMS, and email MFA
Multi-tenant user and application management
Event-based workflow customization through webhooks and Lambdas
Strengths
Enterprise features built in: Includes multi-tenancy, advanced MFA, and SSO without requiring separate services.
Flexible deployment: Offers both managed hosting and full self-hosting for infrastructure control.
Protocol coverage: Supports modern and legacy SSO standards for broad compatibility.
Ideal for
Teams that want a powerful, extensible identity platform with options for self-hosting or cloud deployment. FusionAuth is a suitable Stytch alternative for organizations that need deeper enterprise capabilities and more control over how identity services are deployed and customized.
Which Stytch alternative is right for your app?
There are many quality alternatives to Stytch. The 8 we’ve covered are among the best, and each has its own unique pros and cons that might make it a better or worse fit for your needs. The best way to choose the right option for your app is to consider your biggest issue with Stytch. Which of the alternatives does the best job of solving it?
Here’s a quick reference guide based on the primary pain points discussed above:
If you want auth and security features, consider Auth0, Keycloak, or Descope.
If you want multi-tenant management, consider FusionAuth, Keycloak, or Descope.
If you want integration flexibility, consider Ory Kratos, Supabase, or Descope.
If you want smooth, sustainable scalability, consider Cognito or Descope.
In all of these cases, multiple Stytch alternatives can work. However, Descope covers a broader range of needs than most alternatives here, especially for teams that want authentication, authorization, multi-tenancy, and orchestration in one platform.
Choosing the best Stytch alternative
Stytch offers a clean developer experience and strong passwordless capabilities, but many teams eventually reach its limits as their applications grow. Multi-tenant requirements, enterprise SSO, advanced orchestration, and connector-driven workflows often reveal gaps that lead developers to consider other platforms. The alternatives in this guide provide a range of options that address these needs in different ways, from fully managed services to customizable open-source systems.
Among the available choices, Descope stands out for its unified B2C and B2B platform, visual workflow editor, and broad set of connectors that simplify identity implementation and ongoing management. By handling authentication, authorization, and orchestration in a single system, Descope helps teams focus on building their products instead of maintaining identity workflows.
Sign up for a Free Forever account with Descope and start building secure, scalable auth flows today. Have questions about enterprise features and scalability? Book time with our experts.