Table of Contents
About Darwinium
Modern applications continue to deal with threats like account takeover (ATO), fake account creation, and automated abuse. Attackers use automation tools, proxy networks, device spoofing, and sometimes even real people to bypass standard security. They try stolen credentials in large numbers, set up fake accounts, exploit promotions, and target valuable transactions while appearing legitimate. If authentication lacks behavioral and device intelligence, organizations face a higher risk of unauthorized access, fraud, and ongoing account problems.
With the Descope Darwinium Connector, developers can add real-time device checks and behavioral risk scoring to authentication and user journey flows. By checking device integrity, user behavior, and risk at signup, login, and other key points, teams can block fraud before it starts and still give trusted users a smooth experience.
About Darwinium
Darwinium is a fraud-prevention and risk platform built to proactively detect and block both automated and human-driven attacks across the customer journey.
The platform checks device integrity, looks for spoofing signals and unusual behavior, detects automation tools and virtual environments, and flags network issues and device reuse across sessions or accounts. This helps security teams spot suspicious patterns, even if attackers change IP addresses, spread out their activity, or try to hide automation.
Darwinium helps prevent account takeover, spot fake or synthetic accounts, stop credential stuffing, reduce promotion and transaction abuse, and find slow, distributed automation. When used with Descope, these risk signals turn into real-time decisions in adaptive authentication, allowing user journeys to adjust as attack methods change.
Connector overview
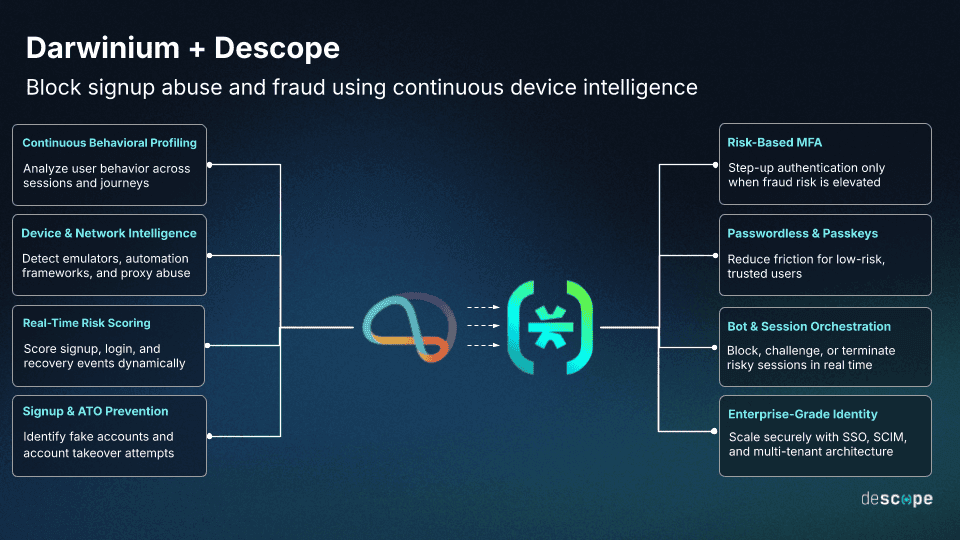
Darwinium performs real-time behavioral risk analysis and device profiling to identify fraud across authentication and high-risk user journeys. The Descope Darwinium Connector integrates Darwinium’s risk intelligence directly into Descope Flows through two primary signal layers:
Behavioral and risk signals
Continuous behavioral analysis that detects:
Interaction anomalies inconsistent with legitimate users
Automated or scripted journey execution
Suspicious network and proxy usage
Velocity inconsistencies and low-and-slow activity
Signals associated with account takeover and synthetic identity abuse
Darwinium aggregates behavioral and contextual telemetry into a unified risk assessment that distinguishes trusted users from automated and human-assisted fraud attempts. Out of the box, Descope can send web-based interaction signals such as typing speed and browser behavior to Darwinium during authentication flows to help generate this risk assessment.
Device profiling
Persistent device intelligence that identifies:
Compromised or spoofed browsers and environments
Headless browsers and automation frameworks
Emulators and virtualized infrastructure
Tampered or modified client environments
Cross-session device reuse patterns
Cross-account device correlation linked to fraud rings
Darwinium generates a durable device profile that persists across sessions, enabling detection of repeat fraud infrastructure even when attackers rotate IP addresses or distribute activity over time. Device-level signals are enabled by integrating the Darwinium SDK directly in the application, allowing the device data to be evaluated alongside Descope flow signals for deeper risk analysis.
The Descope Darwinium Connector integrates directly into Descope authentication workflows and can be orchestrated alongside step-up MFA, identity verification, IP intelligence, and custom business logic to enforce adaptive, risk-based user journeys.
Use case: Prevent account takeover through device and behavioral profiling
Account takeover attacks increasingly combine automation, residential proxy networks, and human intervention to compromise legitimate users. Attackers test stolen credentials, replay sessions from emulated environments, and pivot across accounts using shared fraud tooling. According to the Cifas Fraudscape 2025 report, account takeover cases jumped 76% in 2024, with telecom and online retail platforms hit the hardest. Because the credentials and session flows often appear valid, traditional authentication systems struggle to distinguish real users from attackers operating with breached data.
Darwinium checks device identity, unusual behavior, and links between accounts to spot takeover attempts, even if attackers change IP addresses or spread out their activity.
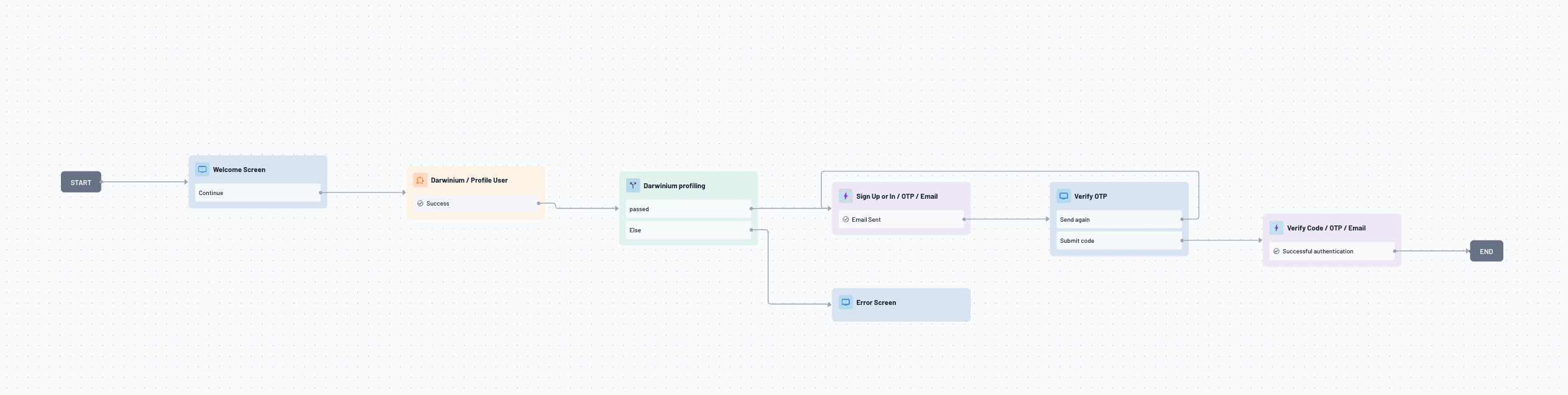
Here’s how a Descope Flow works with Darwinium during a login attempt:
The user submits credentials for authentication.
Descope checks the login details and starts Darwinium profiling at the same time.
Darwinium reviews the device’s security, looks for signs of spoofing, and compares user behavior to past patterns.
Darwinium sends back a risk score and suggests what to do next.
The Descope Flow then decides whether to allow the login, ask for extra verification, or block and record the attempt.
This approach identifies repeat fraud infrastructure and suspicious behavioral shifts while minimizing friction for legitimate users signing in from trusted devices.
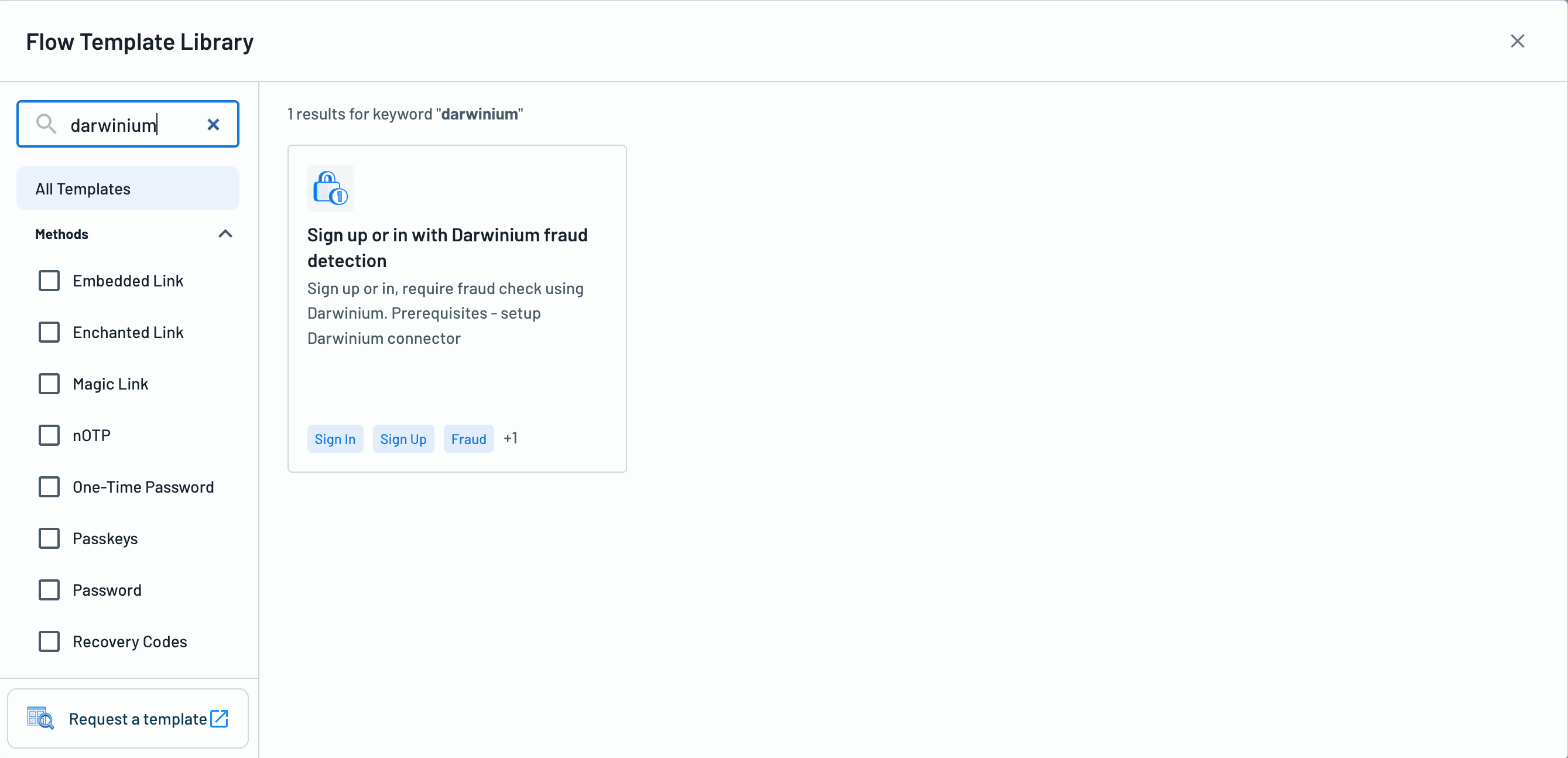
Get started today by using the Sign up or in with Darwinium fraud detection Flow Template, available directly in the Descope Console.
Use case: Prevent fake account creation and synthetic identity abuse
Fraud groups often make many fake or automated accounts to take advantage of promotions, abuse free trials, prepare for future account takeovers, or game platform rewards. They spread these attacks out over time and use proxy networks to avoid detection.
Darwinium finds automated signups, accounts made with emulators, device spoofing, and repeated device fingerprints across new accounts. This reveals organized fraud behind what look like separate registrations.
Here’s how a Descope Flow works with Darwinium during registration:
A user starts to sign up for an account.
Descope runs Darwinium profiling before finishing the account creation.
Darwinium checks the device’s security, looks for signs of automation, and reviews the device’s history across sessions.
Darwinium provides a risk score along with details about possible fraud.
The Descope Flow then decides whether to allow the registration, ask for more verification, or block and record the attempt.
This device-focused and behavioral approach stops large-scale fake account creation, while keeping onboarding easy for real users.
Conclusion
The Descope Darwinium Connector delivers production-grade fraud prevention across authentication and high-risk user journeys, enabling security teams to detect and stop account takeover, fake account creation, and distributed automation without heavy custom engineering. By embedding Darwinium’s device profiling and behavioral risk signals directly into declarative Descope Flows, developers can implement adaptive, risk-based controls that evolve alongside changing attack tactics.
If you haven’t yet started your Descope journey, sign up for a Free Forever account and set up your own Darwinium connector. To explore other connectors, visit our integrations page.