Table of Contents
What is biometric authentication?
You can unlock your iPhone with your face. Your bank verifies million-dollar transfers with a thumb scan. Yet somehow, countless sensitive accounts still rely on traditional credentials, which can be as weak as “Password123!” According to the Verizon DBIR, 88% of attacks in 2024 against basic web applications involved stolen credentials, highlighting an imminent need to evolve beyond legacy authentication techniques.
Enter biometric authentication, which identifies users based on who they are rather than what they know, and is quickly becoming the gold standard in user authentication. 72% of people worldwide preferred face verification for secure online transactions in 2022, and more than 50% of all users authenticated with biometrics daily in 2024.
But what is biometric authentication, how does it work, and is it actually that safe? Let’s find out if it’s the right authentication method for your app, website or software.
Main points
Biometric authentication shifts the paradigm. Instead of relying on knowledge or possession, it verifies users by who they are—making it harder to fake, steal, or forget.
Users want convenience without compromise. Adoption is soaring because biometrics offer seamless, fast, and secure experiences that reduce friction and abandonment.
What is biometric authentication?
Biometric authentication is a type of inherence-based authentication that validates a person’s identity using their unique biological or behavioral characteristics. These characteristics make up “what” or “who” you are—often referred to as the inherence factor in authentication lingo. This shift from “what you know” (knowledge factor) or “what you have” (possession factor) represents a move from vulnerable, perishable credentials to intrinsic human traits that are virtually impossible to replicate.
The core principles of biometric authentication are as follows:
Uniqueness: Every person’s biometric traits are distinct. Fingerprint patterns, facial geometry, iris structure, and vocal characteristics are as individual as DNA. Even identical twins have different fingerprints and iris patterns!
Permanence (or immutability): Unlike passwords, biometric traits don’t change significantly over time. Barring serious injury, biometrics remain consistent throughout life, making them reliable long-term identifiers.
Measurability: Advanced sensors can capture and digitize these characteristics into strings of data. While humans might compare fingerprints visually, machines verify biometrics against what are essentially long sets of numbers, which both protects biometric data from being copied, and ensures a highly precise comparison.
Universality: Nearly everyone possesses the basic biometric traits (fingerprints, face, voice) necessary to authenticate, making the technology widely applicable across global populations.
Acceptability: Ideally, the collection and use of biometric data doesn’t raise concerns or objections from users; it should be convenient and unintrusive (e.g., not a DNA swab).
Consider a real-world example of biometric authentication in action using Apple’s Face ID. When first set up, infrared sensors project over 30,000 invisible dots to form a depth map of the user’s unique face, measuring the precise distance between the eyes, the curve of the nose, and the contours of the cheekbones.
This creates a mathematical model stored in a dedicated part of the user’s device called the Secure Enclave. Each time the user looks at their phone to unlock it, the system captures a new scan, compares it to the original stored template, and grants access when everything matches.
Biometric authentication methods
There are multiple types of biometric authentication in use today, with ongoing research to develop new and more sophisticated approaches. The most prominent types include fingerprints, facial anatomy, iris/retina scans, and voice authentication.
Fingerprints
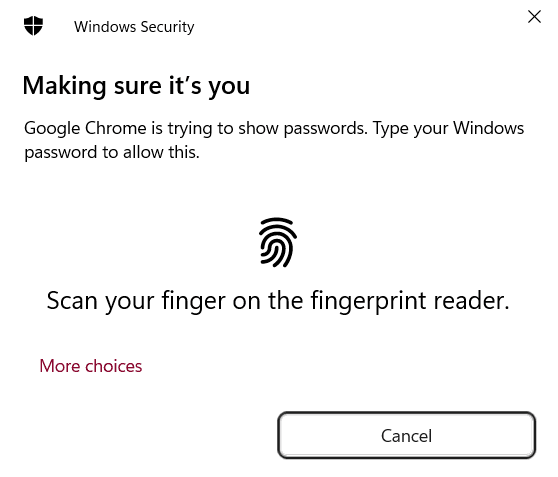
Fingerprint authentication uses the unique ridges and patterns of a person’s fingerprint to validate their identity. The proliferation of electronic devices with fingerprint scanners has made this one of the most widely adopted biometric methods.
Facial anatomy
With the prevalence of laptops, tablets, and mobile devices equipped with cameras, facial recognition has become a popular biometric authentication method.
Facial recognition systems analyze the unique characteristics and geometry of a person’s face to confirm their identity. Each human face has around 80 nodal points, including the distance between the eyes, the width of the nose, and the length of the jawline.
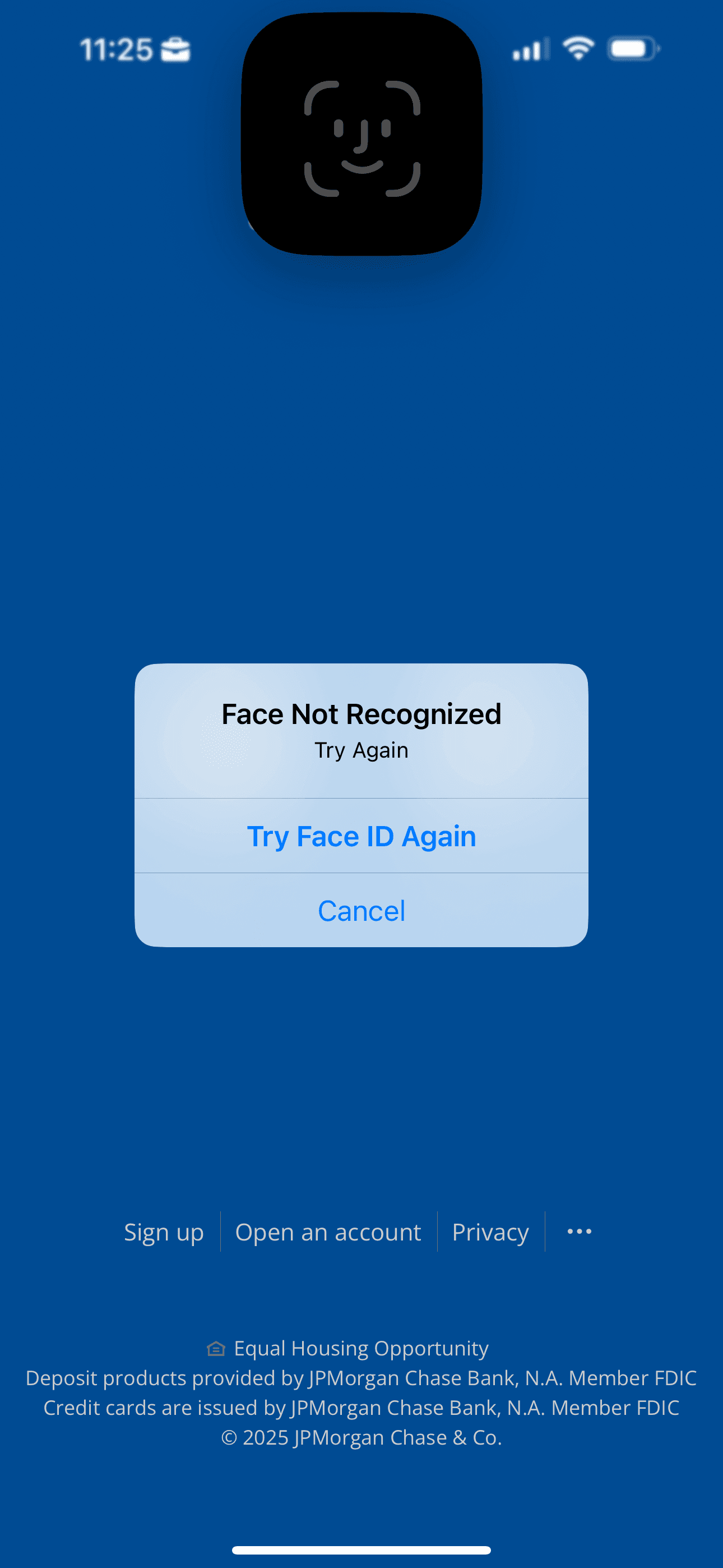
Scanners convert these nodal points into a faceprint or an encrypted digital model. Advanced systems also perform “liveness detection” to prevent spoofing attempts using static images.
Iris/retina scans
Iris and retina scans involve the analysis of unique eye features for authentication. Retina scans analyze the distinctive pattern of blood vessels around the eye, while iris scans analyze the colored rings found within the iris. Iris scanners collect nearly 240 biometric identification features for precise authentication.
Eye scans are accurate but tricky to implement because they need infrared light sources, compatible cameras, and low-light conditions.
Voice authentication
Voice recognition technologies analyze the unique tone, pitch, and accent of a person’s voice to validate their identity. Physical traits such as the shape of the nose and the length of the vocal tract determine a person’s voice, making it a viable authentication factor.
Like with facial recognition, voice authentication systems can use liveness tests for additional security to prevent spoofing attempts.
Multimodal authentication
Similar to multi-factor authentication (MFA), multimodal biometric authentication is an advanced security approach that combines two or more biometric identifiers to verify a user's identity.
By simultaneously utilizing various biometric traits, such as fingerprints, facial recognition, voiceprints, or iris scans, this method aims to overcome the limitations and vulnerabilities associated with single-modal biometric systems.
Multimodal biometrics is a compelling authentication method for organizations requiring heightened security. It significantly enhances security and reduces the risk of unauthorized access, making it more challenging for malicious actors to breach security systems.
Emerging biometric authentication methods
In addition to established biometric technologies, several emerging methods are gaining ground:
Gait recognition. Gait recognition systems use a person's manner of walking to validate their identity. Factors such as step length, stride, foot and hip angles, and gait cadence are considered in this form of authentication.
Vein recognition. Vein recognition systems analyze the unique pattern of blood vessels in a person’s hand or finger to validate their identity. When implemented correctly, vein recognition offers exceptional accuracy. Notably, Amazon Go stores employ a form of vein recognition in their palm scanners for shoppers.
Keystroke. Keystroke recognition systems, or keystroke dynamics, track patterns in how an individual types. Like all behavioral biometrics, this approach isn’t as reliable as inherent traits for identifying a person on its own, so it’s better suited to supplemental verification. However, recent studies show promising results, with over 70% reliability with some models.
How biometric authentication works
To understand how biometric authentication secures the user’s digital identity, let’s follow the journey of a fingerprint scan on a smartphone, from the moment the user first sets it up to each daily unlock.
Core components
Biometric systems rely on three essential components working in harmony:
Sensor: Captures the user’s biological data (capacitive scanners for fingerprints, infrared cameras for faces, microphones for voice)
Storage: Securely stores their biometric template locally on their device or in encrypted databases
Processor: Compares new scans against stored templates using sophisticated matching algorithms
Raw data vs. templates
When the user first registers their fingerprint, the system doesn’t store a raw image. Instead, it extracts unique characteristics: ridge patterns, minutiae points (where the ridge lines end or fork), and spatial relationships. These patterns are converted into a mathematical model, typically 1-2 kilobytes of encrypted data stored in a secure environment. Their actual biometric data (the high-resolution fingerprint image) is captured, processed, and immediately discarded. Only the mathematical representation, known as a template, is kept for later comparison.
The template creation process involves one-way transformations and feature extraction that result in significant information loss. While it’s not technically impossible to rebuild a fingerprint image from a template, the gaps in data make an attempt computationally difficult. Meanwhile, the pixel-level detail needed to reproduce actual ridge patterns simply isn’t there anymore.
On-device vs. server-side storage?
Once the biometric template is created, the next decision is where to store it. Modern implementations increasingly favor on-device storage, where the template stays within a secure enclave or trusted execution environment (TEE) on the user's device. This setup keeps biometric data local to the hardware, which reduces the risk of interception or mass data breaches.
In contrast, server-side storage involves transmitting the biometric template to a centralized database for storage and matching. While this approach can simplify multi-device authentication or enterprise-wide management, it also creates a high-value target. A breach could expose many users’ biometric templates at once—data that, unlike passwords, cannot be changed.
On-device storage aligns more closely with privacy-by-design principles and is now the standard for consumer devices like smartphones and laptops. It supports faster authentication, reduces network dependencies, and makes spoofing attempts significantly harder by keeping matching operations local to the device. This is why technologies like Apple’s Touch ID and Face ID, as well as Android’s BiometricPrompt API, are built around on-device processing.
The present and future of biometric authentication
Let’s shed some light on some key factors driving the rising prominence of biometric authentication approaches.
Biometric scanners are in everyone’s hands – literally
This widespread accessibility to biometric scanners is reshaping how individuals interact with their digital world, making authentication more seamless and secure than ever before.
The global popularity of smartphones with built-in fingerprint and facial recognition have brought biometric authentication into the mainstream. As major tech companies like Apple, Google, and Samsung continue to refine and expand their biometric offerings, adopting these technologies is expected to skyrocket in the coming years.
Password challenges
The prevalence of passwords in online activities has introduced user friction and security challenges. Users often struggle to create and remember strong, unique passwords for multiple accounts. Forgotten passwords lead to user drop-off and complex reset procedures. Reusing passwords across accounts elevates the risk of credential stuffing and account takeover.
In contrast, biometric authentication provides a more secure and convenient alternative. Fingerprint or face recognition scans are quicker than typing passwords and eliminate the need for users to remember complex passwords, reducing user churn and drop-offs.
The passkeys revolution
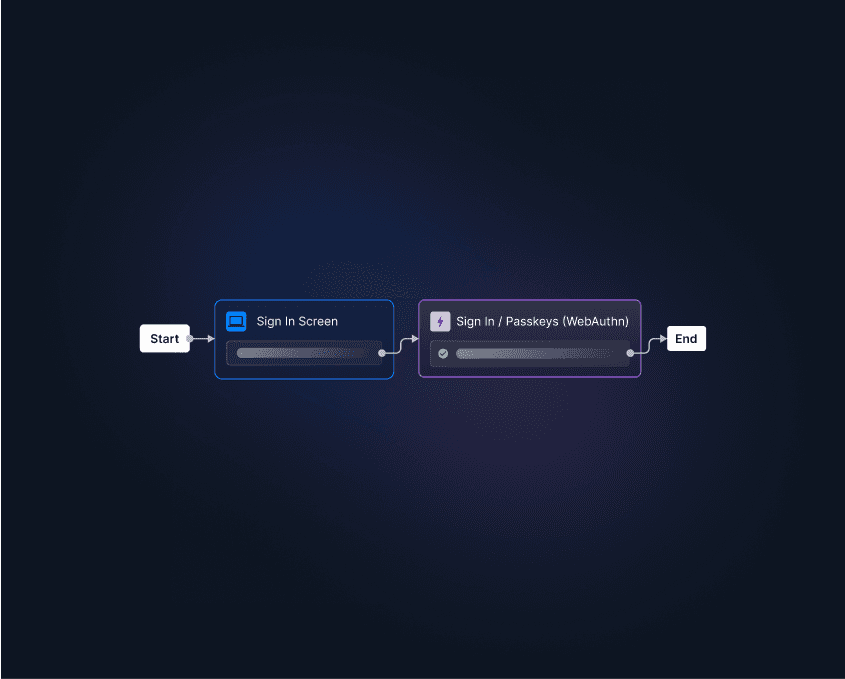
Biometrics-enabled devices ignited biometric authentication, while the Web Authentication API (WebAuthn), Fast Identity Online (FIDO2) and passkeys are accelerating its adoption.
Here’s how it works: passkeys are an authentication method based on FIDO2, an open standard built on WebAuthn and the Client to Authenticator Protocol (CTAP). Passkeys offer a simple and reliable way to implement these different auth protocols, all in one neat package. Previously, web authentication with biometrics wasn’t as standardized, which made both implementation and onboarding or educating new users difficult.
Passkeys have skyrocketed in adoption, and everyday users are embracing them at an unprecedented rate. According to a 2025 report from the FIDO Alliance, 75% of global consumers have heard of passkeys, 69% have enabled them on one or more accounts, and nearly half (48%) of the top 100 websites now offer passkeys as an authentication method.
Looking for a way to test your WebAuthn flows? Check out Virtual WebAuthn, a set of Go tools that help developers test WebAuthn flows without needing a browser or an actual authenticator.
Privacy protections
Privacy concerns surrounding biometric authentication have led to the enactment of various privacy acts and regulations.
During the 2023 legislative session, multiple states (including Arizona, Hawaii, Maryland, Massachusetts, and others) have introduced approximately 15 biometric privacy law proposals. These proposals seek to establish new regulations governing the collection and use of biometric information, encompassing data like retina scans, fingerprints, and voiceprints.
Modeled after Illinois's Biometric Information Privacy Act (BIPA), these bills include provisions for private actions and damages, potentially increasing compliance requirements and liabilities for companies handling biometric data. Given the fragmented regulatory landscape, businesses should ensure their data practices align with these evolving laws, especially if they deal with residents of states considering BIPA-like legislation.
FIDO Certified biometric authentication solutions prioritize privacy even further. They ensure that biometric information is never stored on servers; instead, it is encrypted and locally stored on the user's device.
Also read: Passwordless Authentication 101
Pros and cons of biometric authentication
Biometric authentication is the key to enhanced security and user convenience, but like any technology, it comes with its own set of advantages and considerations.
Advantages of biometric auth
Enhanced security. Biometric authentication, rooted in "who users are," is significantly more resistant to theft and misuse than passwords, PIN codes, and other knowledge-based authentication methods. Using biometric authentication based on WebAuthn also ensures that user secrets remain secure, reducing the potential attack surface.
Improved user experience. Utilizing a fingerprint scanner or glancing at a camera for biometric authentication is considerably faster than manually entering credentials. Additionally, biometric authentication doesn’t require users to create and memorize passwords, reducing churn and drop-off rates.
Widespread adoption. Biometrics are built into everyday electronic devices and used by a wide range of applications. Multiple surveys have found that users prefer using biometrics over passwords, with 68% citing convenience as the primary reason for their preference.
Considerations of biometric auth
Failed authentication in edge cases. Despite the immutability of an individual's biometrics, certain conditions can result in failed authentication. For instance, fingerprint sensors may not function well with wet or dirty hands, or voice recognition may fail if the user has a sore throat.
Potential training data bias. Training data for biometric authentication systems has historically been biased toward white males, leading to identification inaccuracies in women, people of color, and other underrepresented groups. Tech companies are actively addressing this issue and striving to make improvements.
Inability to reset biometrics. Unlike passwords, which can be changed if compromised, biometric data cannot be altered if stolen. Consequently, it is vital to store user biometric data locally rather than on centralized servers.
Biometric authentication use cases
Here are some examples of how different biometric methods are used nowadays.
| Fingerprints | Facial Recognition | Retina/Iris | Voice Recognition |
|---|---|---|---|---|
Identity verification | ✔ | ✔ | ✔ | ✔ |
Financial transactions | ✔ | ✔ |
| ✔ |
Computer security | ✔ | ✔ |
| ✔ |
Law enforcement | ✔ | ✔ |
| ✔ |
Smartphone unlocking | ✔ | ✔ |
| ✔ |
Passport/Visa verification | ✔ | ✔ | ✔ | |
Airport security | ✔ | ✔ | ✔ | |
Ecommerce security | ✔ | ✔ | ||
Healthcare patient ID | ✔ | ✔ | ✔ | |
Ecommerce payments | ✔ | ✔ | ||
Attendance tracking | ✔ | ✔ | ||
Access control | ✔ | ✔ | ||
Mobile payments | ✔ | ✔ |
| ✔ |
Vehicle unlocking | ✔ | ✔ | ||
Safes and locks | ✔ | |||
Social media tagging |
| ✔ |
No / low code biometric auth with Descope
Biometric authentication is shaping a more secure and convenient digital world. With biometric scanners now common in our devices, technologies like fingerprint recognition and facial analysis are revolutionizing how we access information. The global biometric market is booming, highlighting trust in this approach.
Descope helps developers easily add biometrics to their apps with no-code workflows. This includes capabilities such as:
Using biometrics for strong MFA.
Adding passkey authentication, including autofill and backup capabilities.
Promoting biometrics as a second factor after user registration.
Sign up for a Free Forever account to start using Descope today. Have questions about our platform? Book time with our auth experts.