Table of Contents
Where MFA adoption actually stands
Multifactor authentication (MFA) trends show that adoption is already widespread and continuing to expand into more applications and user journeys. But having MFA and having effective MFA are not the same thing. Effective MFA requires full coverage across applications, phishing-resistant methods that remove shared secrets, and enforcement that adapts to risk. Without these, MFA can still leave meaningful gaps.
While most organizations have some form of second factor, far fewer have one that holds up against modern attacks.
The question today isn't whether to use MFA. It's which methods are actually resilient and why the gap between deployed and phishing-resistant MFA remains so wide.
Below, we’ll explain what the landscape of MFA looks like in 2026 and beyond, covering:
Where companies are in terms of MFA adoption
Why older MFA approaches are losing ground
What new, adaptive MFA looks like in practice
Where MFA adoption actually stands
MFA adoption is growing across both consumer-facing and enterprise applications. However, even where MFA is widely deployed, SMS OTP and knowledge-based methods still dominate, despite their weaknesses.
Per our 2025 State of Customer Identity Study, 94% of organizations have some form of customer MFA. But just 10% of them offer MFA across all their applications, and about a third (32%) have a mix of protected and unprotected apps. About a quarter (24%) cover just a handful.
To ensure effective MFA, coverage, not presence, is the actual measure worth considering. And even coverage alone isn’t enough. Method choice determines how well that coverage holds up under real-world attack conditions.
That being said, not all MFA is created equal. The prevalence of MFA bypass attacks in recent years is evidence that some forms of MFA are less secure than others. In particular, attackers exploit SMS-based one-time passwords (OTPs) and knowledge-based credentials via man-in-the-middle (MITM) and related attacks like adversary-in-the-middle (AITM).
Not all MFA adoption is plagued by potential vulnerabilities or oversights, however. Our study found that 45% of organizations have deployed passkeys in at least one app, and this MFA method is phishing-resistant by design. Another 27% plan to deploy passkeys within two years.
Despite this progress, most organizations still lack effective MFA coverage across all apps.

Another key factor is how MFA methods align with different user groups and application contexts. Our study found that 51% of orgs use workforce identity and access management (IAM) tools for customer auth, but only 8% would choose that approach if starting fresh today, showcasing how MFA tools are often stretched beyond their intended use.
This is especially problematic because workforce IAM platforms weren’t designed for customer-facing flexibility, which limits how easily modern, user-friendly MFA methods can be implemented. For example, methods like magic links are often harder to implement or customize in workforce IAM tools.
Reliance on internal IAM tooling is likely why MFA skews toward legacy methods:
75% of MFA adopters use single sign-on (SSO)
71% use authenticator apps
58% use OTPs
These methods still have value, but they’re more vulnerable when layered on top of passwords rather than replacing them.
Looking ahead, passwordless MFA adoption is accelerating, driven by passkeys and user expectations for faster, simpler login experiences.
Why legacy MFA is losing ground
Legacy MFA is losing ground because it doesn’t hold up against modern attack patterns.
Verizon’s 2025 Data Breach Investigations Report (DBIR) highlights that credential abuse remains the leading initial attack vector — exposing the limits of MFA approaches that still depend on passwords. As long as passwords remain part of the flow, the attack surface stays intact.
Additionally, execution is just as much of a problem as method choice. According to Descope’s study, 39% of organizations reported a security incident tied to weak or missing MFA, while 27% lost revenue after enforcing it. Overall, 82% experienced measurable business impact from authentication issues, including support costs, user drop-off, and lost customer trust after security incidents.
These issues often persist even when MFA is in place.
One of the most common MFA methods, SMS OTP, is vulnerable to the MFA bypass attacks noted above, as well as other weaknesses. Aside from SIM swapping and OTP interception, cybercriminals can also take advantage of push notification fatigue to launch MFA bombing attacks. Or they can leverage previously leaked account details in credential stuffing attacks.
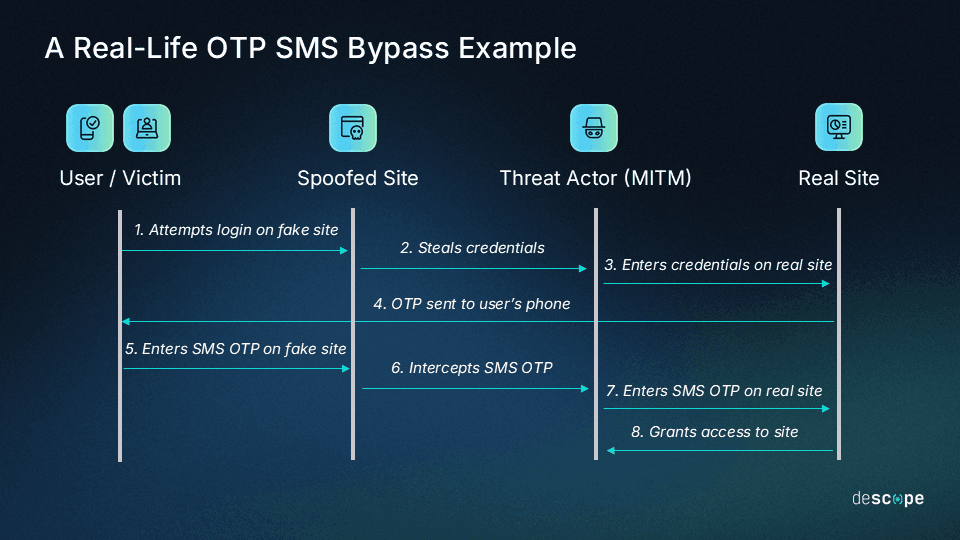
When MFA deployments use less secure methods like SMS OTP, they remain vulnerable to a wide range of attacks, some of which are designed to take advantage of users’ MFA fatigue.
Even with leading security measures, MFA only works when it’s consistently enforced. In the often cited 2024 Snowflake breach, accounts without enforced MFA were exposed — highlighting how gaps in enforcement can undermine otherwise sound controls. In response, Snowflake added features that would require MFA across accounts, while retaining the flexibility to selectively enforce it.
The shift toward phishing-resistant and adaptive methods
As MFA adoption increases and the public becomes more aware of the risks in legacy methods, phishing-resistant MFA and more secure, trustworthy approaches will take over. These approaches combine phishing resistance with adaptive enforcement, reducing friction for low-risk users while maintaining strong security.
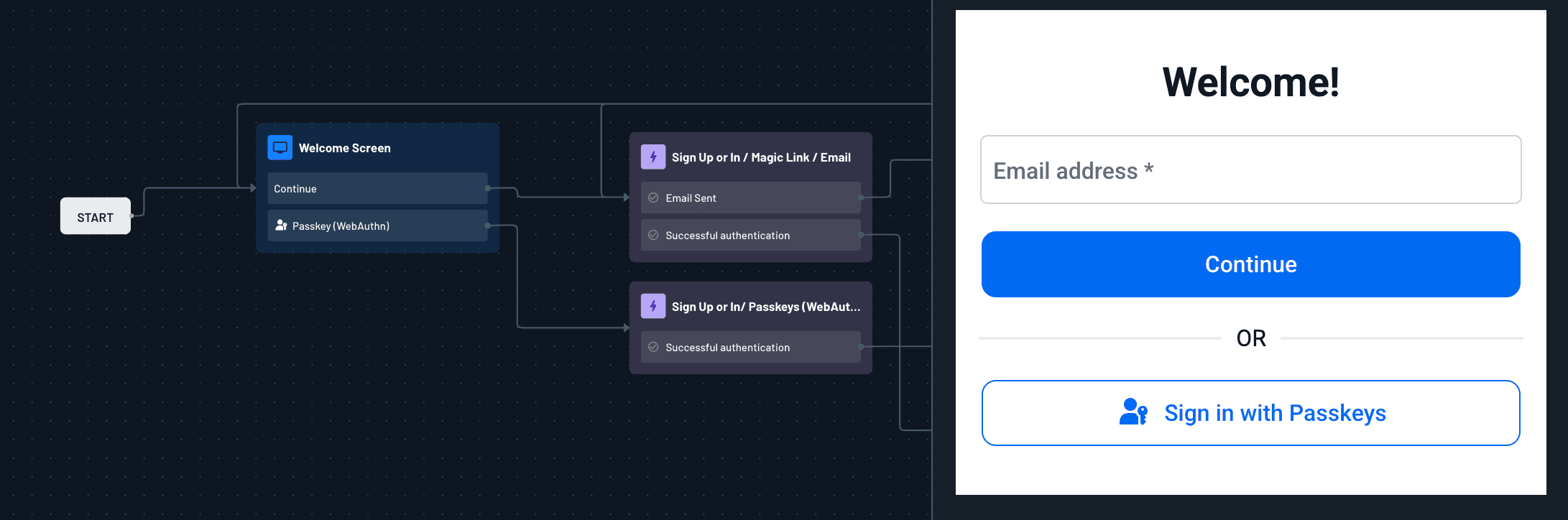
For example, passkeys are single-action MFA by design. They combine something the user has, or a possession factor (a device), with something they are, or an inherence factor (face recognition or fingerprint). Magic links are another popular option, adding a possession-based factor without requiring new hardware — though their security depends on the integrity of the user’s email account.
Also Read: How Branch Reduced Auth Support Tickets By 50% With Passkeys
Adaptive authentication, driven by real-time risk signals, is replacing static second factors. These decisions are driven by signals like device trust, location, behavioral patterns, and session risk. With modern MFA, step-up authentication can be configured to trigger a second factor only when signals warrant it rather than on all login attempts. This reduces friction for low-risk everyday sessions while raising the bar when it counts.

Platform momentum is normalizing this shift to modern MFA solutions. For instance, new Microsoft accounts are passwordless by default, and Microsoft reports that 99% of users who start the passkey signup process complete it. Apple and Google are following suit, moving toward passkey-first systems. Additionally, the 2025 FIDO Report found that 75% of global consumers are now aware of passkeys, and the majority of those consumers agree that passkeys are both more secure and more convenient than passwords.
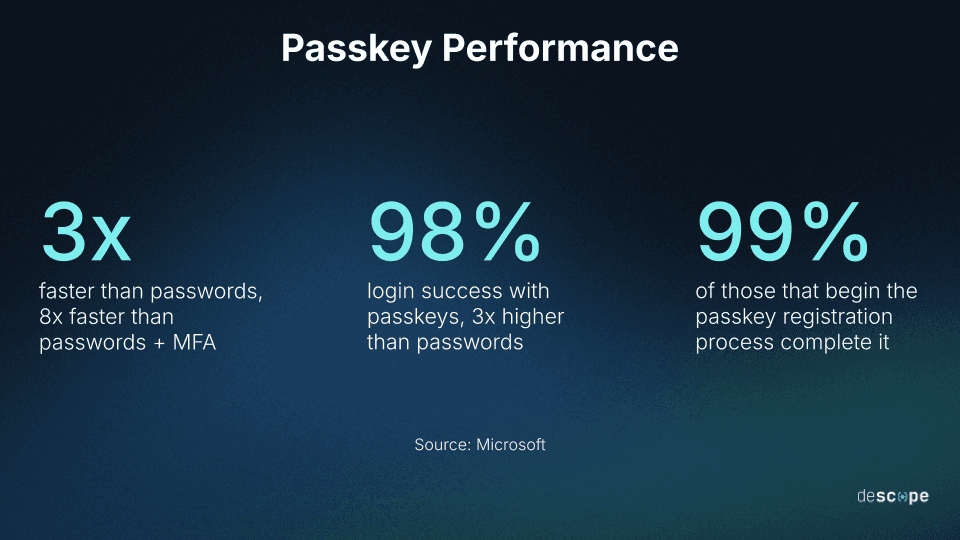
For organizations, these advanced MFA deployments don’t just ensure reliable security. When properly configured, they promote a stronger UX, offering the speed and efficiency that influences customer satisfaction and loyalty.
Another example is Navan, a multinational business travel and expense management company that implemented fast, secure, and phishing-resistant MFA. In particular, Navan needed to implement email magic links that allowed customers to securely log in to and manage their accounts. But implementation needed to happen without added friction. By leveraging Descope Flows and the platform’s interoperability with SAML and OIDC, Navan set up magic links in four days, without major changes to their existing system.
Stay ahead of MFA trends with Descope
The underlying trend in MFA adoption is not just more MFA—it’s smarter, better MFA. Method selection matters just as much as having a second factor to authenticate users beyond a username and password.
Looking ahead, the practical path is incremental. Orgs positioning themselves for success will layer phishing-resistant methods onto existing flows, use progressive rollouts, and treat auth as a product metric alongside a security one. A/B testing auth flows and finding the right balance between security and smooth UX will be the key to leading rather than catching up to MFA trends.
Implementing this shift requires flexible orchestration across user journeys, applications, and risk levels.
Descope is a powerful, flexible customer identity and access management (CIAM) platform that helps teams implement phishing-resistant and adaptive MFA without rebuilding their auth stack. Our full-feature suite is accessible to all teams with no- and low-code visual workflows.
Sign up for a Free Forever account with Descope and start building secure, scalable auth flows today. Have questions about adaptive authentication or phishing-resistant MFA? Book time with our experts.






