Table of Contents
Passwordless authentication by the numbers
Passwordless authentication replaces knowledge-based credentials (passwords) with possession- or biometric-based methods such as passkeys, magic links, and social login.
In 2026, passwords are still everywhere despite these superior alternatives. According to the Descope State of Customer Identity 2025 survey, 87% of orgs still use password-based auth for customer-facing apps, yet only 2% believe passwords effectively balance security and UX.
State of Customer Identity 2025
Get identity insights from 400+ customer IAM decision-makers.
Get your copy
The data we’ve collected confirms what other industry authorities like Fast Identity Online (FIDO) have found: Passwordless is no longer in the distant future. Consumer awareness is at an all-time high, enterprise adoption is accelerating, and the methods have matured significantly.
The challenge in 2026 is not whether to go passwordless, but how to get there from where you are without disrupting what already exists. In this guide, we’ll explain why that is, covering:
Where passwordless auth stands today
Why passwordless auth is taking over
How passwordless auth is evolving
Where passwordless auth is heading
Passwordless authentication by the numbers
The strongest indicator that passwordless authentication is the future—if not the present—is that end-user awareness of passwordless authentication has hit a new high and is set to keep rising.
Passkeys are the best barometer for passwordless adoption. While magic links, email one-time passwords (OTPs), and OAuth social login are all notable password alternatives, most stats focus on passkeys because they represent a fundamental shift in auth philosophy. Per
FIDO's World Passkey Day Report 2025, 75% of global consumers are now aware of passkeys.
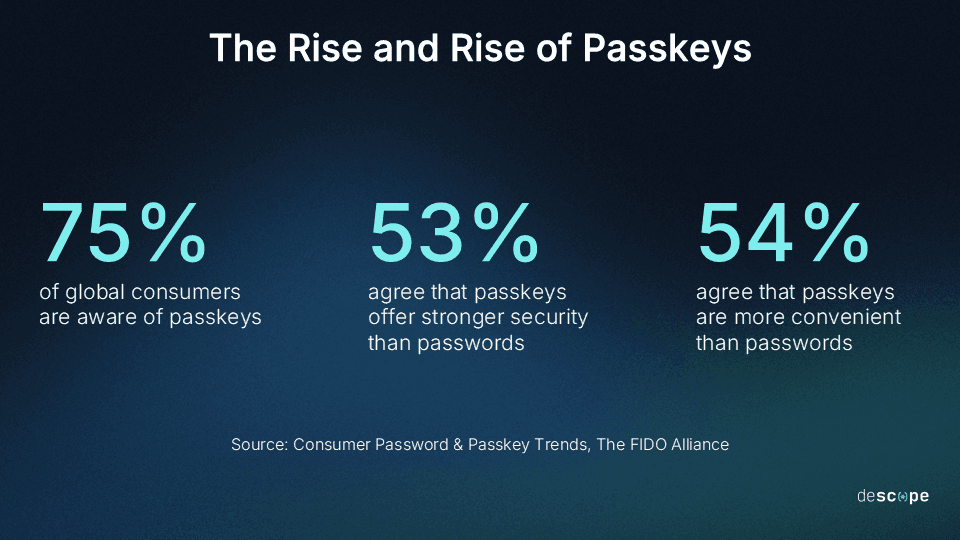
Even more striking is that, among those who know about passkeys, most say they’re more secure than passwords, and a majority agree they’re more convenient. Contrast this with FIDO's 2023 barometer report, in which 23% of users chose biometrics as their preferred authentication method, and 22% rated it the most secure, the top choice in both categories.
Organizational adoption is also gaining real momentum, per our 2026 auth stat roundup:
According to Descope’s own findings, 45% of organizations have already deployed passkeys in one or more apps, and 27% plan to implement within the next two years.
Per FIDO, 48% of the top 100 websites offer passkeys, doubled from the previous year.
Per Dashlane, passkey auth doubled from 2024 to 2025, reaching 1.3M per month.
However, legacy auth still has a firm grip across various industries.
As noted above, our State of Customer Identity study found that, despite the adoption curve and only 2% of orgs calling passwords effective, 87% are still running passwords as part of their auth stack. Additionally, 51% of orgs use workforce IAM tools for customer auth, lacking magic links, email OTPs, and passkeys, but only 8% would choose that approach if starting fresh.
This illustrates the gap between knowing and doing: Organizations know where they’d like to be, but they’re still chained to a system built for a different era. Development woes are a major contributing factor, as 46% of orgs reported postponing CIAM improvements to handle other pressures, and 47% noted they struggle to modernize legacy systems.
Ultimately, all passwordless authentication news points toward it taking over sooner rather than later.
Why the status quo is increasingly costly
The business impact of effective authentication is real and multifaceted. Organizations that implement it reap benefits, and those that don’t often suffer consequences. But if passwordless auth is as good as it seems, why don’t all organizations go passwordless?
The reason is simple: perceived costs of switching, exacerbated by existing auth pressures.
Another key finding from our State of Customer Identity survey is that 82% of organizations reported tangible business impacts from customer authentication issues in 2025. Specifically:
52% of orgs faced increased support costs from auth-related incidents
37% of orgs saw user drop-off from overly complex onboarding
28% of orgs lost customer trust after auth-related security incidents
And the costs cut both ways: We also found that 27% of orgs lost revenue after tightening customer auth, while 29% experienced security incidents after loosening it. For many orgs, it feels as though they’re in a lose-lose scenario when it comes to dialing in their auth approach.
One major pressure on orgs is the fact that customers vote with their wallets and feet.
A deeper dive into FIDO’s 2025 findings shows that about half (~48%) of consumers would abandon purchases due to an authentication issue. This illustrates the direct financial impact that ineffective auth can have. And, in practice, FIDO reports that 36% of consumers did in fact have at least one account compromised due to weak or stolen credentials in the last year.
Beyond causing consumers to abandon purchases, auth issues can also cause users to abandon platforms altogether. According to Sift’s Q3 2025 Digital Trust Index, 75% of users abandon a platform after an account takeover (ATO) incident. Additionally, 87% of users spread negative word-of-mouth, which is part of why Sift projected $17 billion in ATO losses for year-end 2025.
Given this context, it’s unfortunate that threats to credentials have never been more profound.
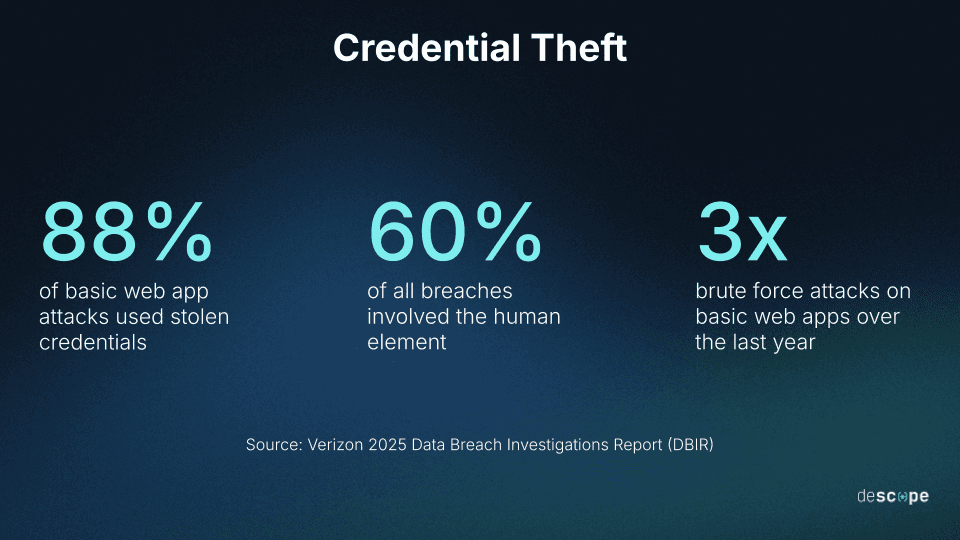
In 2025, researchers at Cybernews unveiled that over 19 billion passwords had been exposed in breaches between April 2024 and 2025. Of that staggering figure, a commanding majority (94%) were reused or duplicated across accounts, but that doesn’t diminish the scale of the issue. And while not all compromises lead to direct consequences, 2.8 billion passwords were available on criminal boards in 2024, per Verizon’s Data Breach Investigations Report 2025.
A major factor behind this massive spike in compromised credentials, per the DBIR, was the growth of brute force attacks, which nearly tripled over the past year. Per Verizon, they grew from 20% to 60% of all Basic Web Application Attacks. Relatedly, 22% of all breaches began with credential abuse, making it the most common initial vector, more than phishing or exploits.
Aside from these inherent threats, implementation complexity compounds the problem and prevents more orgs from adopting effective auth. Per our findings, 51% of organizations rely on developers with minimal auth experience to build customer-facing identity systems.
Auth is a full-time specialization, but most teams are not staffed accordingly.
As a result, security gaps are discovered too late, and UX debt accumulates until it costs customers. The unfortunate reality is that too many companies stick with passwords because they assume that DIY or assisted upgrades are beyond their expertise and resources.
How passwordless authentication is evolving
Passwordless authentication is not a monolith—never was, never will be. At base, it’s a family of auth methods that can be deployed incrementally, layered, and combined into any bespoke solution to fit an org’s needs. It will continue to grow in sophistication in 2026 and beyond.
Some of the most common and effective tools used in passwordless auth solutions include:
Passkeys – These are a gold standard in passwordless auth. Whether based in FIDO2, WebAuthn, or another protocol, they offer phishing-resistant, device-bound credentials that work similarly to how a user unlocks their phone. Passkeys leverage biometric auth as a login method, making for single-action multi-factor authentication (MFA) by design by simultaneously checking for something the user is (their retina) and has (a phone).
Magic links – These are one-click, link-based authentication tools delivered via a trusted channel like email. They remove password friction and eliminate memorization entirely. While not inherently phishing-resistant like passkeys, they significantly reduce credential-based risk and can be layered into adaptive MFA flows for stronger protection.
One-time passwords (OTPs) – Despite the name, OTPs are not actually passwords. Instead, OTPs are limited-lifespan, one-time “passwords” sent via email, SMS, or cycled as a time-based one-time password (TOTP) in an authenticator app. They’re widely understood, easy to deploy, and useful in layered passwordless MFA flows.
Social login – This method allows users to sign in using a secondary account such as Google, Apple, Facebook, LinkedIn, or GitHub. Social login delegates auth to a trusted provider and reduces friction in consumer-facing apps, maintaining security and UX.
, showing the Acorns logo at the top and a centered message with the heading Your login code, text stating Thank you for verifying your identity. Your unique login code is followed by a five digit code 19531, and a note below indicating that account security is a priority and recommending changing the password if this was not initiated by the recipient, displayed within a standard email client interface.](/_next/image?url=https%3A%2F%2Fimages.ctfassets.net%2Fxqb1f63q68s1%2F2xUsJ7RqeZAuwyJt3s0O2P%2F8deb2e6c06a927ba44a50b2f7ce8c32b%2FEmail_OTP_example.png&w=3840&q=75)
When using powerful, flexible auth platforms, organizations can implement as many (or as few) passwordless methods as they need to meet users where they are while strengthening security.
Real orgs are adopting these methods incrementally—layering passwordless options into existing stacks without ripping out legacy systems:
Navan achieved auth success by working with Descope to develop a magic-link-based passwordless MFA. This resulted in fast, secure, and frictionless auth specifically because the solution met users where they already were (email) while raising the security floor.
Branch Insurance augmented their auth with passkeys using Descope, dramatically reducing support overhead. Branch saw a high degree of customer support being dedicated to password resets and login issues, which passwordless auth eliminated.
The bottom line is that passwordless authentication is often additive, not a replacement. It meets real security needs without requiring a mass migration strategy before teams are ready.
Where passwordless authentication is heading
Looking ahead, passkeys and passwordless auth will become table stakes rather than just differentiators. As noted above, passwordless news shows us that consumer awareness is at an all-time high. The benefits and continued evolution indicate that business demand will follow.
Organizations that deploy passwordless authentication now have a unique opportunity to open up a window, impressing customers early, before passkey support becomes an expectation rather than a luxury. The competitive pressure will only grow as more top sites adopt.
The immediate future should feature lots of hybrid auth, not a complete handoff.
In all likelihood, most teams still running password-based auth in 2026 will continue running them alongside passwordless methods into, if not through, 2027. That’s the realistic trajectory, and it’ll be unusual for organizations apart from heavy-hitters to go full passwordless sooner.
However, the platform giants are not waiting, and neither should other organizations. Microsoft, Apple, and Google have all moved toward passkey-first or password-reduction experiences. New Microsoft accounts are now passwordless by default, which the giant is framing as a “simpler, safer sign-in” experience across the board. Google went passwordless by default in 2023, and, while Apple has not made this change (yet), it supports user uptake of passkey-based auth.
For most orgs, the practical path will be incremental. Rather than immediately abandoning passwords altogether, consider adding options for passkeys or magic links and using A/B testing to see how users respond. Prioritize these new auth solutions in new apps, and use progressive rollouts to move your existing users into any new protocols with little to no forced migration.
Whatever you do, don’t forget about MFA. Adaptive, risk-based, "step-up" auth is replacing static second factors, and methods that eliminate passwords are the go-to for this use case.
Fortunately, we know that the user side is already here.
Most users want passkeys as an option, even if there’s some reasonable concern by orgs around messaging and adoption. Microsoft has “convinced a billion users to love passkeys,” reporting that 99% of users who start the passkey signup process finish it. And, on the business side, auth is increasingly a product and conversion metric, not just a security gate. That applies equally to B2C and B2B organizations, where UX and security can both make a big difference with buyers.
The outcomes for orgs that adopt are real and measurable. Passkeys three times faster than passwords, eight times faster than passwords and traditional MFA, lead to login success three times more often than password-based auth (98% vs. 32%), per Microsoft. And these user outcomes translate to lower support costs upfront and over time.
Importantly, going passwordless does not need to mean ripping out your entire auth stack. The incremental, additive approach often works best—both for orgs and for their end customers.
Optimize your auth today with Descope
Passwordless authentication will undoubtedly be a big part of the future of auth, in large part because it’s already taking over. User awareness and adoption are at all-time highs and continue to grow, traditional auth methods are becoming unsustainable, and passkeys and other passwordless methods are becoming better and more efficient over time.
To meet the moment and stay ahead of shifting expectations, organizations need more than a new login method—they need infrastructure built for change.
Descope enables teams to implement passwordless authentication through visual, no- and low-code workflows, layer it alongside existing systems, and adapt flows over time, without rebuilding authentication every sprint.
Sign up for a Free Forever account with Descope and start building secure, scalable auth flows today. Have questions about passwordless authentication? Book time with our experts.