Table of Contents
What is strong authentication?
With most businesses now having a digital presence, user identity is the new battleground for cybercriminals.
From November 2023 to April 2024 alone, there were nearly seven billion known records of data breaches in the U.S. The vast majority of these breaches stem from stolen credentials. This is why strong authentication processes are so critical.
Authentication processes typically employ username-password combinations to grant access to an application. Strong authentication processes step in when simply a password won’t be enough for identity validation. By using a combination of passwordless methods and risk identification, strong authentication raises the bar for attackers looking to gain unauthorized access to systems.
In this guide, we’ll dive into everything you need to know about strong authentication, why it’s so important, and recommended methods and best practices to keep your data secure without adding undue user friction.
What is strong authentication?
Strong authentication may look different from one organization to another, but its overall purpose is the same. That is to make authentication processes more robust by requiring multiple steps and making it more difficult for adversaries to crack. The concept is based on the premise that providing multiple forms of evidence of the user’s identity makes it much harder for unauthorized access.
Multi-step authentication processes give you stronger protection against potential threats. If one identifying step is somehow compromised, the others still remain intact. Strong authentication methods typically leverage at least two factors of the following:
Something the user knows: This includes passwords, PINs, or other knowledge-based factors that the user has memorized.
Something the user has: These are possession-based factors, such as security tokens, smartphones (used for receiving one-time passcodes via SMS, email or running authentication apps), smart cards, or key fobs.
Something the user is: These inherence factors are associated with the user's physical traits, and they involve biometric verification methods such as fingerprint scans or facial recognition.
Possession- and inherence-based factors are usually the ones adding the “strong” to strong authentication since knowledge factors are easily exploited.
Initial account creation using strong authentication may take a little extra time, but it’s crucial for ensuring the protection of your confidential data. However, users have grown used to this multi-step strong authentication and actually prefer it because it keeps their accounts secure.
Importance of strong authentication
While a username and password combination remains to be the most popular authentication method, it poses a low barrier to entry for cyberattacks. This is especially true if passwords are weak, used across multiple accounts, or contain easily accessible information like birthdays or names. Believe it or not, the most commonly used password is “123456”.
It can also be shockingly easy for usernames and passwords to be shared, which makes them even more vulnerable. Among a group of IT professionals surveyed, 53% said they use email to share passwords with colleagues. Cybercriminals are skilled—sharing passwords to sensitive accounts via email is almost like serving them access on a silver platter.
Considering that stolen credentials and web application attacks account for well over 80% of all data breaches, the importance of strong authentication cannot be understated.
Strong Customer Authentication (SCA)
Strong Customer Authentication (SCA) is a rule that went into effect in 2019 as part of the Payments Services Directive 2 (PSD2) regulation in Europe. It requires certain changes to how your European customers can authenticate online payments.
If your business is impacted by this regulation, three things are true: You are based in the European Economic Area or you create payments on behalf of accounts based in the EEA, you serve customers in the EEA, and you accept credit or debit cards. If transactions do not meet SCA guidelines, they may be declined by your customers’ banks.
Recommended strong authentication methods
We recommend introducing a number of different passwordless authentication methods into your strong authentication strategy:
Phishing-resistant MFA
Most users are familiar with multi-factor authentication (MFA) which uses at least two factors to verify user identity. Phishing-resistant MFA is an approach that accounts for MFA vulnerabilities, like prompt bombing or MFA bypass attacks. It requires authentication factors that cannot be easily stolen or replicated by cybercriminals.
Biometrics
Biometric authentication validates a user’s identity based on unique physical or behavioral characteristics. These include fingerprints, facial features, eyes, and voice. Even with the increased accuracy of deep fakes, biometrics offer enhanced security and convenience as these traits are still extremely difficult to forge or steal.
Passkeys
Passkeys are a newer way for user authentication without requiring a password. They are part of the WebAuthn / FIDO2 set of specifications, creating a cryptographic key pair (public and private keys) for authentication. The private key stays on the user's device, while the public key is shared with the service provider. Users authenticate with a PIN or biometrics.
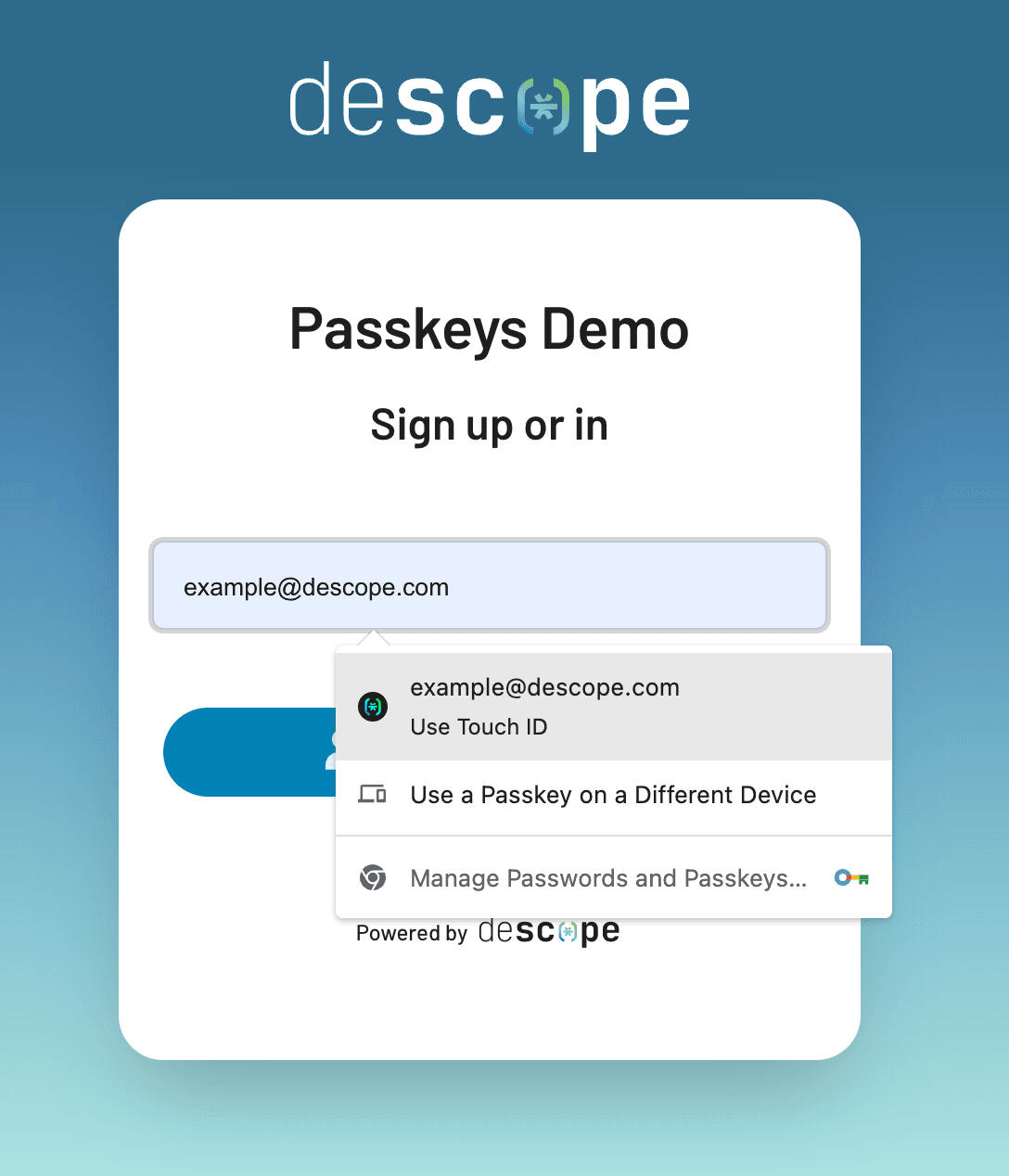
Passkeys are designed to be both phishing-resistant and easy to use.
Strong authentication best practices
Here are several key best practices to keep in mind when deploying and maintaining strong authentication.
Adaptive authentication
Adaptive authentication is seen as a reinforcement of standard MFA, which requires the same set of identifying factors every time. With adaptive authentication, the number and type of factors required depends on the risk present during login, like an unrecognized device, unknown network, or time of login.
Regular review and update of auth policies
Strong authentication can only be successful if you consistently monitor your policies and their enforcement and effectiveness. Technology and security threats are always evolving, so your strong authentication must be able to adjust and keep pace with them.
Organizations that don’t have the budget or bandwidth to continually adjust their authentication security controls can choose to invest in CIAM solutions purpose-built for fraud prevention.
Staying compliant with regulation
Adopting strong authentication is about more than protecting data and user privacy. There are also regulatory compliance requirements set by governments or other regulatory bodies that must be met to stay in operation. Some common compliance regulations include:
HIPAA: A US healthcare regulation ensuring the privacy of patients and their sensitive information.
SOC 2: Ensures companies securely manage and protect customer data.
PCI-DSS: Governs how credit cards are handled to protect against fraud, including changing default passwords.
User education
It’s important for all users—employees, customers, admins, and developers—to have a strong understanding of not only how strong authentication works but also why it matters. It’s also critical to ensure that users are following all rules and guidelines when it comes to protecting sensitive information.
Layered security
Security measures are most effective when used in layers. Each layer of security you implement adds an extra line of defense and makes it much harder for cybercriminals to get into your network. Combine strong authentication with other security measures (such as encryption, security audits, and access controls) to create a comprehensive security strategy.
No single security measure is foolproof, so layering different types of security can help protect against a range of threats.
Drag-and-drop your strong authentication with Descope
Strong authentication, while crucial, is complex to set up and maintain. To take the burden off of your developers, Descope’s intuitive CIAM platform lets you drag-and-drop your preferred strong authentication methods in a workflow. You can also check for a variety of conditions upon login – such as VPN usage, native and third-party bot scores, and new devices – and route the login attempts to different paths in your user journey.
Sign up for a Free Forever account with Descope and build your strong authentication flow with minimal coding. Have questions about our platform? Book time with our auth experts.