Table of Contents
What is MFA bypass?
As developers integrate more advanced methods to authenticate users, cybercriminals implement new strategies to overcome those security measures. These include exploiting multi-factor authentication (MFA), which requires users to verify their identity through two or more methods.
While MFA mitigates many of the security issues involved with single-factor authentication, there are multiple techniques cybercriminals use to bypass it.
In this blog, we will explore the prevalent methods and discuss different ways to help you prevent and mitigate MFA bypass attacks.
What is MFA bypass?
MFA bypass is a form of cyberattack that can use different techniques to overcome the preset security measures within a multi-factor authentication flow to access an account. Bypassing MFA is a significant security threat, defeating the purpose of having multiple layers of security protecting a system or application.
In 2023, Kroll observed a growing number of cyberattacks targeting 90% of organizations that already had MFA in place. Furthermore, Cisco Talos reports that in the first quarter of 2024, 50% of their incident responses involved MFA bypass attacks.
So while MFA remains one of the most secure authentication solutions, it is not immune to attacks and organizations need to take measures to minimize the threat and attack surface, which we’ll talk about shortly.
Methods for bypassing MFA can vary widely, including social engineering attacks, exploiting vulnerabilities in the implementation of the MFA process, intercepting or redirecting communication containing authentication factors, sim swapping, and using malware or credential stuffing to compromise one or more authentication factors.

Six common MFA bypass techniques
Attackers use various techniques to bypass MFA, exploiting both technological weaknesses and human factors. While new methods continually emerge, some of the most prevalent techniques include:
1. MFA fatigue
MFA fatigue attacks, also known as prompt bombing, involve harassing users with repeated authentication notifications. Once an attacker secures an end user’s credentials, they can repeatedly trigger authentication requests to the user’s secondary authentication method. Attackers use the high volume of push notifications to wear down the user until they confirm the authentication request.
Users may assume that an alarming amount of MFA push notifications is the result of a glitch or malfunction, not realizing that a cybercriminal has gained access to their login information. Victims of fatigue attacks may also be so overwhelmed by notifications that they’re willing to do anything to stop them, especially if the deluge of calls or texts makes their phone more difficult to use.
This can result in the acceptance of a fraudulent authentication request, giving the cybercriminals full access to their account.
2. Session hijacking
In session hijacking, attackers steal cookies that store data from a legitimate user authentication session and exploit those cookies to access an account. Because cookies store authentication data, attackers using session hijacking can anonymously take over an active session without encountering an MFA checkpoint.
While authentication cookies are only valid for a limited timeframe, experienced cybercriminals leverage this opportunity window to bypass MFA and exploit a real login.
There are multiple techniques cybercriminals can use to steal the cookies they need for session hijacking. These can include implementing:
Malware
Packet sniffing
Proxy servers that mirror a real website
3. Man-in-the-middle
Man-in-the-middle attacks are a type of session hacking in which cybercriminals direct users to a proxy server, intercepting their login credentials and session cookies. Like other session hijacking methods, man-in-the-middle attacks gain access by taking over the account after a legitimate login from the end user.
The proxy server allows the attacker to steal session information and transfer cookies to their own browser, successfully circumventing the MFA process.
Man-in-the-middle attacks typically start with a phishing email or text that tricks users into clicking a link to a proxy server. The proxy server simultaneously gives users access to the target site and impersonates it. Only a minor change in the URL differentiates the man-in-the-middle site from the real one.
Advanced versions of this attack can intercept and use OTPs in real time.
4. Social engineering
The MFA process often involves sending an OTP to the end user’s email or phone and prompting them to enter it. However, cybercriminals can use social engineering to compel users into sharing that code, giving them access to the account.
Attackers use various psychological manipulation techniques, and may pose as friends, family members, financial institutions, or tech support professionals to gain the trust of their victims.
Attackers can also send unrelated emails to the target to gather sensitive information, then contact service providers directly, pretending to be a user who’s been locked out of their account.
5. SIM swapping
Calls and texts are common secondary authentication methods, which causes attackers to target their victims' phone numbers. With SIM swapping, cybercriminals persuade a user’s mobile carrier to move the user’s phone number to the attacker’s device.
Typically, they’ll call the mobile carrier while impersonating the end user and claim that they want to transfer the number to a new phone or SIM card.
Because mobile carriers often seek some form of identity verification before assigning an existing phone number to a new SIM card, cybercriminals often pair SIM swapping with phishing or other forms of social engineering.
Once the attacker has successfully posed as the end user and taken over their phone number, they can approve all authentication requests from their own device and lock the user out of the account.
Read more: Introducing single-click WhatsApp authentication
6. Brute force attacks
Attackers can evade MFA by brute force attacks – attempting various password combinations until they achieve a successful match. The effectiveness of these attacks depends on using simple password combinations as an authentication factor, like a temporary 4-digit PIN, which is less difficult to decipher than a complex alphanumeric combination.
A successful brute force attack compromises an authentication factor, bringing attackers closer to account takeover.
Preventing and mitigating MFA bypass attacks
Although MFA has certain security gaps, it ultimately provides another layer of protection for your users when their first authentication factor is compromised. By implementing safeguards against common MFA bypass methods, you can also mitigate potential security issues and prevent broken authentication.
If your application uses MFA, these strategies can help protect your users and decrease the severity of bypass attacks:
Implement biometric authentication: Face scans and fingerprints are typically more difficult for cybercriminals to replicate, making biometrics a highly secure additional authentication method.
Institute strong password policies: MFA bypass attacks often focus on accounts that use passwords as the first authentication method because of their inherent vulnerabilities. Compromised passwords were the root cause for over 82% of data breaches in 2022. By enforcing strong password policies, you can reduce the likelihood of your users becoming a target.
Adopt passwordless authentication: Keeping passwords as the first authentication factor greatly weakens the integrity of the overall MFA process. Passwordless MFA (where both factors are based on possession or inherence) is a stronger starting point for your MFA implementation.
Restrict login attempts: Limiting the number of push notifications your application can trigger allows you to thwart MFA fatigue attacks. By automatically locking accounts that send a suspicious number of MFA prompts in a short period of time, you can protect your users from overwhelming push notifications and stop compromises in progress.
Use secure authentication methods: Incorporating phishing-resistant MFA, such as FIDO2 authentication, helps protect against social engineering attacks.
Zero Trust Architecture: Adopt a Zero Trust approach where users and devices are continuously verified throughout a session, not just at the initial login. Ensure users have the minimum level of access necessary for their roles to limit the impact of a compromised account.
Implement fraud detection controls: Monitoring user signals and account activity with fraud detection helps you determine when attackers are targeting your users. By deploying step-up authentication or adaptive authentication you can quickly respond to threats or mitigate their impact when account compromises occur.
Conduct regular security testing: Routinely assess your MFA protocols, including the security of OTPs and MFA recovery methods.
Secure your multi-factor authentication with Descope
MFA offers a strong line of defense, but it is not without fault. By using security best practices and controls that anticipate common MFA workarounds, you can seamlessly authenticate real users and keep cybercriminals at bay.
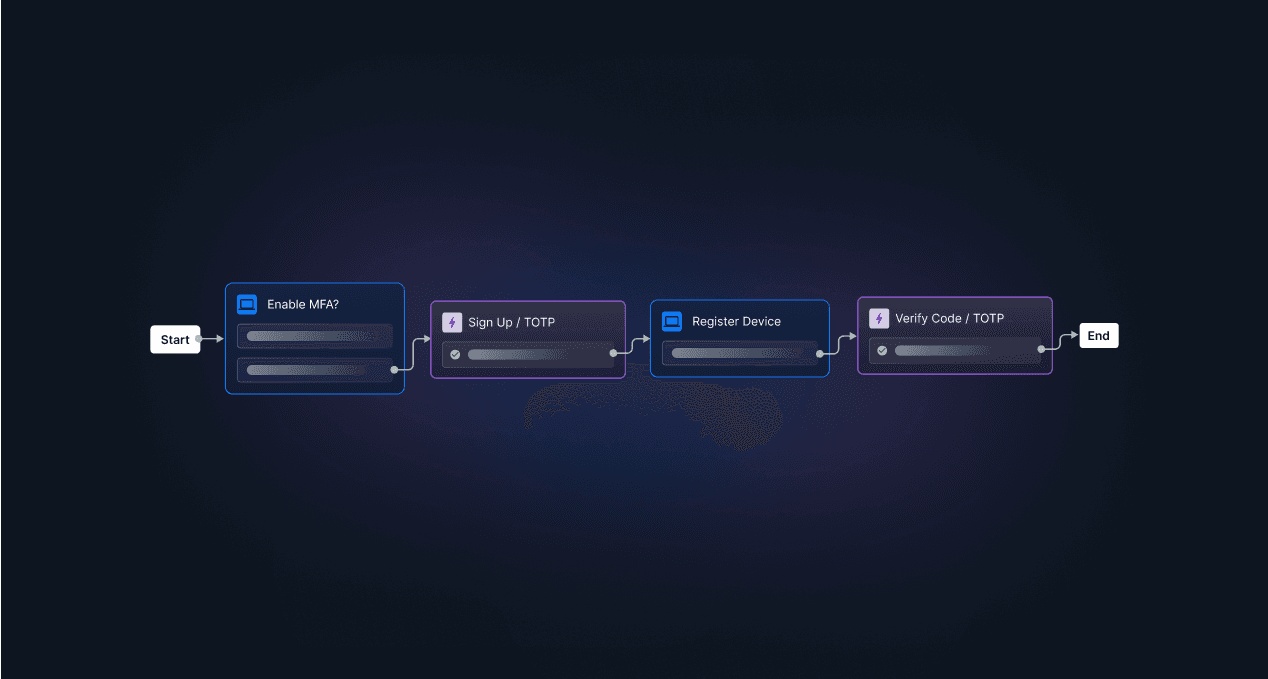
Descope, an MFA provider, helps developers easily add MFA to their authentication flows with drag-and-drop workflows, SDKs, and APIs. Our platform also enables apps to identify risky user signals and add risk-based authentication or step-up authentication to existing user journeys.
Sign up for Descope to remove the complexity from your MFA implementation and gain the ability to “add the right amount of friction” to reduce the likelihood and impact of MFA bypass. Have questions about our platform? Book a demo with our team.