Table of Contents
What is authentication?
When a customer logs into your app, two critical security checks happen in succession. First, your authentication system questions, “Is this a legitimate user or a possible threat?” Second, it asks, “What exactly should they be allowed to see and do?” These two distinct processes, known as authentication and authorization, form the most fundamental foundations of modern identity and access management (IAM).
Broken authentication leads to fraud, account takeover (ATO), and customer drop-offs. Mess up authorization, and you’ll face regulatory fines for exposing private data to the wrong people, or worse, allow a threat actor to assume admin privileges unchecked.
This guide clarifies the interwoven relationship between authentication (authN) and authorization (authZ), shows how they work together to protect customers, and explores how modern approaches like adaptive authentication can stop threats without adding friction to your customer experience.
Main points
Closely related identity processes: Authentication validates identity (who you are), while authorization (what you can do) controls access
Modern auth requirements: AuthN and authZ play important roles in securing identities, with methods ranging from biometrics to tactics like fine-grain authorization
Working hand-in-hand: Authentication happens first to confirm identity, then authorization determines permissions based on roles or attributes
What is authentication?
Authentication is the process of confirming that someone is who they claim to be. Think of it as the digital equivalent of checking someone’s ID at the airport—except instead of a security agent scanning a driver’s license and checking for an outbound flight, your system evaluates credentials like passwords, biometrics, and one-time codes.
In a customer identity flow, authentication happens at the very beginning, before a session begins. When users attempt to log in, your auth system challenges them to prove their identity through one or more factors (i.e., knowledge, possession, and inherence). Only after passing this identity check can they proceed into your application.
For example, when a customer logs in to their online banking account, they might enter a username and password, then receive a one-time code on their phone. The bank’s system confirms these credentials match what’s on file (and what was generated for this specific login) before allowing access. This multi-layered approach, known as multi-factor authentication (MFA), significantly reduces the risk of breaches.
Factors of authentication
Authentication methods use at least one of three main categories of authentication, known as factors. These are often combined for stronger security. Notably, using two methods leveraging the same factor is still considered multi-factor authentication, but it’s generally considered less secure than mixing factors across methods.
Knowledge-based authentication uses something you know, like a password or security question. This can also be a one-time password (OTP), but because these codes are sent to a specific device, can also be considered a form of the possession factor.
Possession-based authentication uses something you have. This could include OTPs, but is generally thought of as physical devices like smartphones with authenticator apps and physical tokens like YubiKeys. Magic links, too, signify ownership of a digital possession
Inherence-based authentication uses something you are. These are innate characteristics, like facial recognition and fingerprint scans, voice authentication, or even behavioral patterns. Biometric scanners are installed in the vast majority of modern smartphones, making the inherence factor an easy choice for high-security logins.
Common authentication methods
Authentication methods have evolved significantly over the years, becoming more sophisticated as the threat landscape has become increasingly complex. Here are some of the most common authentication methods used today:
Passwords: Most common but insecure, password-based authentication involves a secret phrase that the user must enter to gain access. Despite being widely used, it is often considered less secure.
OTPs: A single-use code often sent via SMS or email. More secure than static passwords as they are much harder for attackers to reuse or guess.
Authenticator apps: These apps, such as Google Authenticator or Authy, provide a more secure alternative to SMS-based OTPs because the codes are generated on the user’s device and not sent over potentially insecure networks.
Magic links: Magic links are unique, one-time-use URLs sent to the user’s email address as a method of authentication. It’s an increasingly popular passwordless authentication method.
Physical tokens: USBs or smart cards that store digital certificates or other forms of identification and require insertion or a touch on a reader device to grant access, offering a high level of security against remote attacks.
Biometrics: Biometric authentication uses unique physical or behavioral characteristics for identification, such as fingerprints or facial recognition, providing a high level of security and convenience
Passkeys: The newest standard using device-based cryptographic keys, phishing-resistant passkeys can secure authentication using a PIN or biometric scan on a user’s device. Passkeys are widely supported today, with leading organizations like Amazon and Microsoft leading the drive to adoption.
Single sign-on (SSO) tokens: SSO tokens allow users to access multiple applications or services with one set of credentials, improving convenience and reducing password fatigue.
After confirming the user provided the correct credentials, the next step is to authorize their access.
What is authorization?
While authentication confirms an entity's identity, authorization determines what an authenticated user or service is allowed to do within a system. It is the process that occurs after authentication, providing a way to ensure that an authenticated entity has the appropriate permissions to access resources or perform specific operations.
While authentication answers the question, "Are you who you claim to be?" authorization goes a step further to address, "What are you allowed to do?"
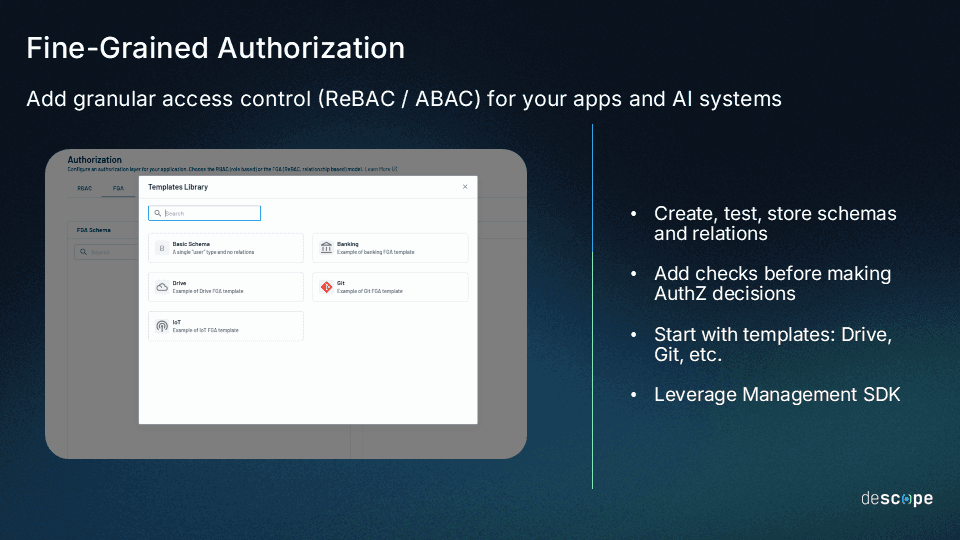
Authorization models
Depending on the organization’s authorization model, access can be granted or denied based on:
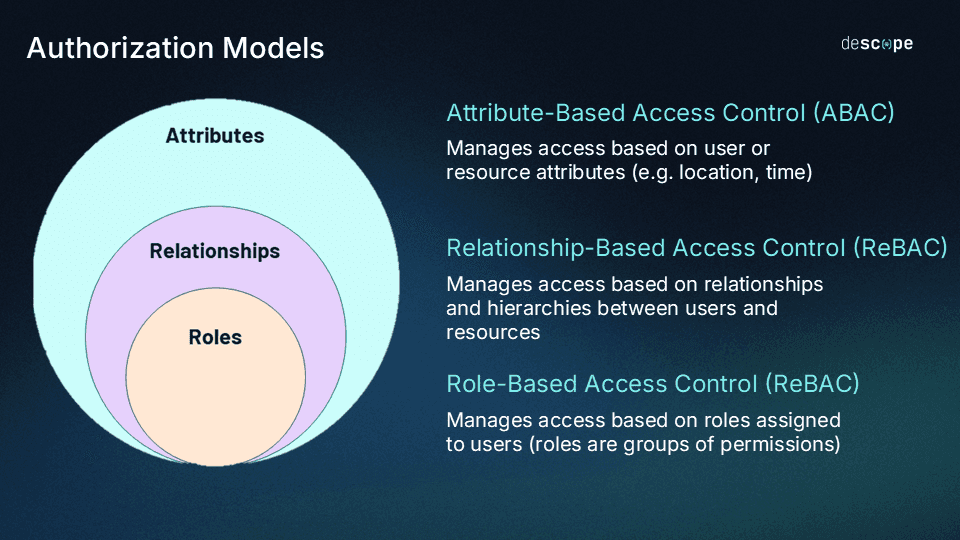
Role-Based Access Control (RBAC): In this model, users are assigned to roles based on their job functions, and each role is granted access to resources necessary for its responsibilities.
Relationship-Based Access Control (ReBAC): In this model, access control is defined through relationships between users and resources (e.g. ownership, inheritance, group membership).
Attribute-Based Access Control (ABAC): ABAC uses policies that evaluate attributes, like location or department of users, to make authorization decisions. This allows for more dynamic and context-sensitive access control compared to RBAC.
Mandatory Access Control (MAC): MAC relies on security clearance to provide data access based on its sensitivity.
Discretionary Access Control (DAC): The opposite of MAC, DAC leaves authorization decisions to the object owner’s discretion.
Learn more: RBAC vs. ABAC: What’s the Difference?
Authentication vs authorization: Differences and relationship
Authentication confirms who the user is, and authorization determines what the user can do.
Authentication and authorization, despite their differences, are integral to the security and functionality of digital systems. They operate in a symbiotic relationship where one complements the other:
Authentication validates user identities: It ensures that users are who they say they are. Without authentication, there's no basis to grant or deny access since the system cannot confirm user identity.
Authorization defines the access level: Once users are authenticated, authorization ensures they can only interact with the parts of the system relevant to their roles or permissions. Without authorization, even authenticated users could potentially access sensitive or critical resources they should not, leading to security risks.
The successful implementation of both authentication and authorization processes is critical for ensuring secure access to resources and systems. By implementing strong authentication and authorization, organizations can protect against unauthorized access, prevent identity theft, ensure compliance with regulations, enable granular access controls, and enhance their overall security posture.
| Authentication | Authorization |
|---|---|---|
Function | Confirming a user's identity | Granting or denying access to a resource |
Purpose | To ensure that only intended users can access a resource or system | To determine what a user is authorized to do once their identity has been confirmed |
Methods | Passwords, biometrics, multi-factor authentication | Permissions, roles, attributes |
Relationship to each other | Authentication is a prerequisite for authorization | Authorization cannot occur without authentication |
How authentication and authorization work together
Authentication and authorization work in a strict sequence: authorization cannot occur without successful authentication first. This dependency ensures your identity system knows exactly who is requesting access to what before decided whether they’re allowed to do so.
Let’s talk through a typical customer flow that showcases both processes working in unison:
Step 1: User attempts to log in
A customer navigates to their banking website
They enter their username and password
The bank’s system checks if the username exists
If it exists, it validates the provided credentials
Step 2: Authentication process
The bank’s system ensures the password hash matches stored information
The system sends a code to the customer’s phone
The customer sends the code, and the system ensures it matches
Authentication success! The system has confirmed this is the right person
Step 3: Authorization takes over
The system checks the customer’s account type: “Junior Saver,” a limited account aimed at teens
Permissions for the account are retrieved based on the authorization policy
The “Junior Saver” is attached to a parent account and can: view its own balance, download statements, and deposit funds by scanning checks
It cannot: make withdrawals, view the parent account’s balance, or open a credit card
Step 4: Session established
The customer is logged in with their specific permissions enabled
Every action they take is checked against the authorization policy
Even though they’re authenticated, trying to access elements outside their permissions will be denied
Benefits of separating authN and authZ
Separating the focus of authorization from authentication provides multiple security benefits:
Deeper defenses: Even if authentication is compromised, authorization limits the potential impact to both users and providers
Principle of least privilege: The broader security concept that users should only be able to access what they absolutely need, and nothing more
Audit trails: Systems can more easily log who accesses what resources and what they tried to do
Auth flexibility: Authorization can be changed without altering authentication methods, and vice versa
For customer-facing applications, this relationship becomes even more vital. A single authentication breach is harmful, but without proper authorization in place, one compromised account could move laterally through an organization to access data from countless others. This is why modern CIAM platforms ensure both processes are implemented correctly and work seamlessly together at scale.
Authentication and authorization with Descope
Authentication and authorization may be distinct processes, but they’re also inseparable. Your organization needs to excel at both to protect your app while providing users with a frictionless experience.
Descope helps developers add authentication and fine-grained authorization to their applications with a few lines of code. Our drag & drop workflows, SDKs, and APIs abstract away auth complexity, while also making it frictionless and secure, so that you can spend more time building your core product.
Particularly, Descope’s passwordless capabilities add an essential layer of security for sensitive environments and data.
Sign up for a Free Forever account to optimize your authentication and authorization flow today. Have questions about implementation with Descope? Book time with our auth experts.