Table of Contents
Why strong healthcare IAM is critical
Healthcare identity and access management (IAM) is critical because of the sensitivity of medical records and the regulatory landscape governing their use. Compliance depends on robust healthcare IAM systems that restrict access to sensitive data and continuously monitor for and prevent unauthorized use—all while supporting, not burdening, healthcare clients.
In the United States, organizations that handle personally identifiable information (PII) related to treatment must safeguard protected health information (PHI) under the Health Insurance Portability and Accountability Act (HIPAA). They may also need to comply with other evolving privacy laws like HITECH, along with local and state-specific mandates, such as the CPRA.
In this article, we’ll discuss how compliance starts (yet often fails) with IAM.
Main points
IAM is foundational to compliance and security. With rising data breaches and strict privacy laws like HIPAA, IAM is a non-negotiable for healthcare organizations.
Authentication must balance security and usability. MFA, passkeys, and adaptive auth help keep accounts secure without disrupting patient or partner experiences.
Modern authorization requires layered models. RBAC, ABAC, and ReBAC work together to grant the right level of access based on role, context, and relationships.
Implementation should prioritize interoperability and consent. IAM systems must integrate across platforms, support mobile flows, and give users control over their data.
SMART on FHIR compatibility ensures compliant authorization. Applying this standard ensures seamless integration with major health record systems like Epic and Cerner.
Why strong healthcare IAM is critical
In healthcare apps, identity and access management (IAM) is the layer that handles how users authenticate (log in) and how your application authorizes access to sensitive resources like patient records, prescriptions, and claims APIs.
As healthcare software has become more digital, interconnected, and patient-facing, the consequences of getting this layer wrong have grown significantly.
Over the past decade, the healthcare industry has seen a dramatic increase in security incidents. In 2014, there were 39 reported breaches; by 2024, that number had surged to 598. The number of individuals impacted rose even more significantly, from under 25,000 in 2014 to over 250,000 in 2024. These breaches compromise patient privacy and can result in serious consequences for organizations involved. HIPAA penalties can exceed $2 million per violation, and reputational damage, remediation costs, and patient churn often add significantly more.
HIPAA is unique among regulations in that it stipulates general protections that need to be accounted for in the Privacy and Security Rules, but gives covered entities freedom in how they satisfy them. For example, while there aren’t prescriptive HIPAA password rules, HIPAA-eligible parties need to ensure that clients’ and other individuals’ identities can be authorized properly.
That’s why IAM must be a central pillar—not an afterthought—for any healthcare organization.
Today’s healthcare ecosystem is increasingly digital, with patients and providers interacting through telehealth, mobile apps, e-prescription platforms, and patient portals. According to recent industry data, 78% of hospitals now offer telehealth services, and patient portal usage has significantly grown in recent years. Each of these touchpoints also introduces new identity complexity: multiple client apps, different user roles, delegated access, and external systems that all need consistent authentication and authorization behavior.
Gartner Report: IAM Adapts to Secure and Enable AI Agents
Get strategic and implementation-oriented guidance for agentic identity.
Get copy
Beyond regulatory compliance, strong IAM enables:
Reduced breach risk with resilient security and well-defined authorization models
Lower incident response costs via rapid account removal and automated policy audits
Faster access to care with secure, seamless onboarding and user-friendly login options
Improved patient trust and satisfaction through consistent identity experiences
Secure collaboration across labs, payers, pharmacies, and other third-party associates
Powerful healthcare identity management helps all stakeholders operate securely, efficiently, and ethically. It prevents breaches while maintaining a smooth user experience (UX) for clients.
Authentication: The first layer of healthcare IAM
In healthcare, authentication isn’t just a technical checkpoint but a critical layer of trust. Whether it’s patients accessing personal records, partners submitting claims, or vendors logging into supplier portals, organizations must ensure that users are who they say they are. Authentication is foundational not just for HIPAA compliance, but for protecting every interaction that touches PHI.
Strong authentication strategies reduce breach risk, streamline access, and uphold patient consent protocols without compromising UX.
Here are the authentication approaches modern healthcare organizations should consider:
Multi-factor authentication (MFA)
MFA requires at least two factors from different categories: something the user knows (password), has (device), or is (biometric). In healthcare, MFA is now considered a minimum standard for PHI protection. It helps prevent credential-based attacks without introducing excessive friction, especially when paired with mobile push or biometrics.
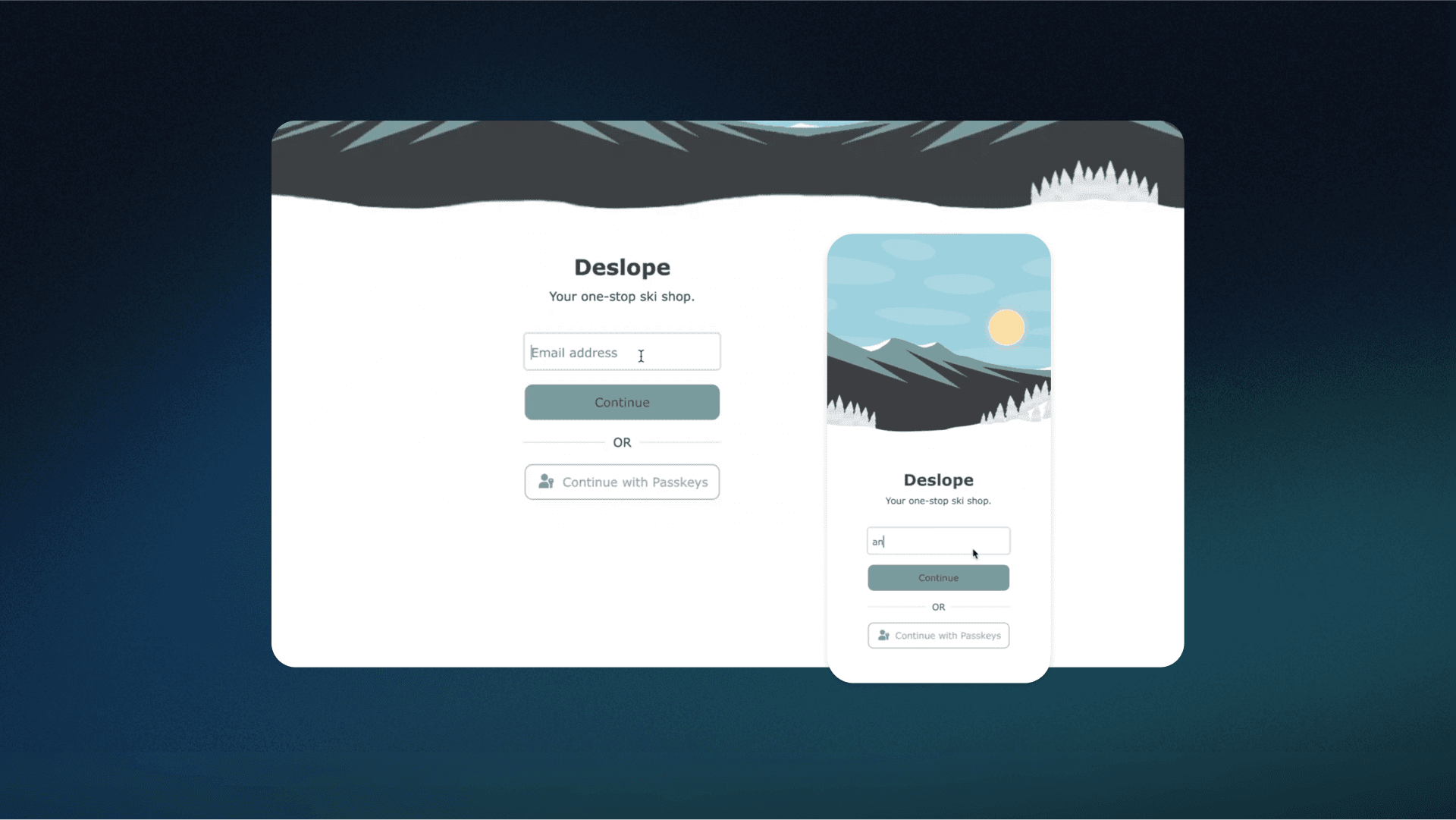
Passwordless authentication
By removing the need for passwords altogether, passkeys eliminate one of the weakest links in healthcare security. Passwordless methods such as device-bound biometrics or authenticator apps streamline the login process while minimizing the risk of phishing and credential stuffing. They also improve the patient and clinician experience by reducing the friction of forgotten passwords.
While passwordless auth is the future, not all healthcare organizations have the infrastructure in place to make the transition yet. For the time being, password management best practices can mitigate the risks associated with credentials. For example, requiring minimum password lengths and/or complexities (i.e., special characters) can help prevent guessing or cracking.
Technological solutions like single sign-on (SSO) or password managers can also help all stakeholders log into and manage their accounts more securely while maintaining UX.
Adaptive authentication
Not every login attempt carries the same risk. Adaptive authentication uses contextual signals like device type, location, access time, and behavioral patterns to assess risk in real time. If the risk is low, login proceeds seamlessly. If anomalies occur, step-up authentication kicks in. This allows healthcare systems to reduce friction for legitimate users while elevating defenses for suspicious behavior.
Identity verification
Authentication confirms you’re the right user. Identity verification confirms you are a real person (and the right one). This is especially critical in healthcare, where patient access often involves uploading a driver’s license, passport, or performing a selfie liveness check.
By integrating identity verification with services like Incode and Amazon Rekognition into authentication journeys, healthcare orgs can verify identities without pushing users to third-party sites or disrupting flow.
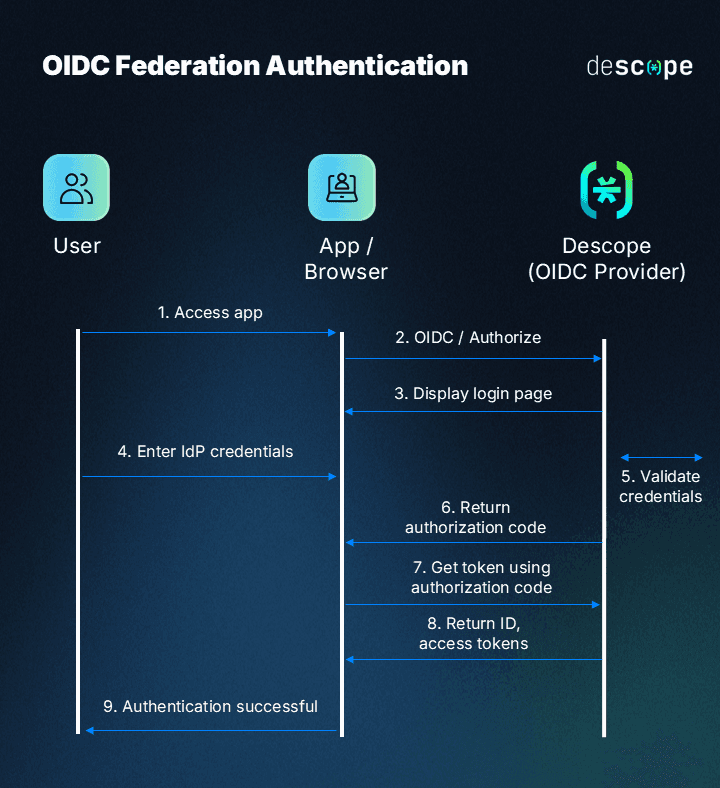
Federated authentication
Healthcare organizations often work with a network of external portals for suppliers, labs, payers, and even internal apps. Federated authentication allows these systems to trust a single identity provider, enabling secure and seamless access across platforms. This centralizes identity management, simplifies UX, and improves visibility across all access points, which is key for governance and auditing.
Authorization: The second layer of healthcare IAM
Once the system confirms a user’s identity through secure authentication, the next step is determining what they’re allowed to access and under what conditions.
That’s where authorization comes in.
In healthcare, authorization governs how patients, providers, partners, and vendors interact with sensitive data. It defines the boundaries: who can access what, when, where, and how. As more users engage with systems across portals, apps, and third-party platforms, managing external access with precision is critical to minimizing risk and maintaining compliance.
To manage this securely and efficiently, organizations can implement a layered authorization strategy:
Role-Based Access Control (RBAC)
RBAC assigns permissions based on predefined user roles, each with an associated access template: pharmacist, lab partner, billing vendor, and so on. This approach is ideal for healthcare scenarios with clearly defined and predictable roles.
For example, a pharmacy partner might have permission to submit prescription data, but no access to diagnostic notes. RBAC enforces the principle of least privilege at scale, helping organizations meet HIPAA and HITRUST requirements with less overhead.
Fine-Grained Authorization (FGA)
Fine-grained authorization enables more granular control than RBAC. FGA’s two implementation patterns are Attribute-Based Access Control and Relationship-Based Access Control. Consent-driven, fine-grained policies enforced by these authorization strategies are crucial for modern patient-centric care models and are often required under data privacy regulations like the 21st Century Cures Act.
Attribute-Based Access Control (ABAC)
ABAC adds contextual awareness by using attributes like user role, location, device, access time, and behavior to determine access rights dynamically. This is especially useful in healthcare, where sensitive data may need tighter controls.
For instance, ABAC can block access to patient records outside business hours or from unapproved geographies. It's more flexible than RBAC and essential for organizations with complex workflows and compliance constraints.
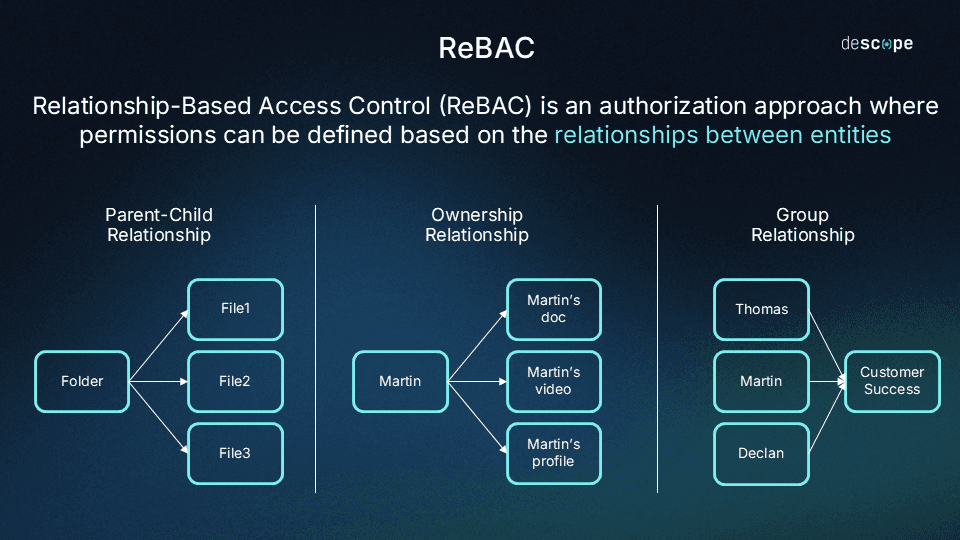
Relationship-Based Access Control (ReBAC)
ReBAC determines access based on relationships between entities, for example, between a patient and their primary care provider, or a caregiver and a dependent. It’s especially valuable in healthcare, where permissions often depend on contextual relationships rather than static roles or attributes. ReBAC enables granular sharing, like allowing a specialist to access only the records of referred patients.
Read more: RBAC vs ReBAC: Which Is Right for You?
Combining models for real-world flexibility
These models aren’t mutually exclusive. In practice, many healthcare orgs implement RBAC with ABAC overlays, using role templates for standard access while layering on dynamic rules (e.g., denying access from outside the U.S. even for authorized roles). This hybrid approach supports scalability while offering the precision needed for patient privacy.
Insider threats in healthcare are a perennial problem. Scientific studies recommend novel approaches to address it, such as implementing machine learning. Another option is leveraging a combination of RBAC, ABAC, and ReBAC to fine-tune auth against attacks from within.
Read more: RBAC vs. ABAC: What’s the Difference?
Integrating IAM With EHR Systems
Healthcare organizations increasingly need their applications to work seamlessly with EHRs like Epic, Cerner, and other clinical systems. SMART on FHIR is the healthcare industry standard that makes this possible. By leveraging OAuth 2.0 and OpenID Connect (OIDC), SMART on FHIR lets apps (and users) securely connect to any major EHR platform.
With SMART on FHIR, healthcare organizations can:
Connect new apps to existing EHR systems without custom integrations
Ensure patients and providers have consistent login experiences across all apps
Meet healthcare compliance requirements for data sharing and interoperability
Reduce development time and costs when building healthcare apps
Instead of building separate connections for each EHR system, SMART on FHIR allows you to use one standard approach that works for every app. That makes it easier to scale your healthcare stack and provide better patient care, everywhere.
Implementation considerations and best practices
Designing and deploying a healthcare IAM system isn't just about choosing the most secure option but it's about balancing security with usability, especially across patient-facing apps and external partner workflows. The best solutions protect sensitive data while keeping the UX intuitive and responsive.
Here are key IAM best practices for healthcare organizations:
Balance security with usability
Patients expect seamless access. Long load times, password resets, or complex login flows create friction and can lead to disengagement or abandonment. That said, convenience can’t come at the cost of security. IAM solutions must provide smooth experiences while resisting phishing, account takeovers, and credential stuffing.
Prepare for evolving threats
Healthcare remains a top target for ransomware, phishing, and supply chain attacks. IAM implementations should prioritize phishing-resistant authentication, device-based trust, and adaptive security policies that evolve with the threat landscape.
One of the best all-around approaches to emerging cyberthreats is “zero trust.” Systems developed with this principle in mind assume that any and all access could be harmful, so all points of interaction require verification. The Cloud Security Alliance (CSA), a proponent of the approach, has noted that zero trust dovetails with IAM strategies like RBAC and ABAC.
Build in consent and privacy controls
HIPAA and modern patient expectations both demand clear consent flows. Patients should be able to manage who accesses their data, when, and for what purpose—and IAM systems should enforce these rules dynamically. All access should be fully logged to support compliance reviews and incident forensics.
Another key part of ensuring seamless consent is continuous, real-time monitoring of PHI access and usage. All sessions involving PHI need to be logged for immediate and longer-term analysis to ensure that patients’ privacy rights are being upheld at all times.
Prioritize interoperability
IAM should work across electronic health record (EHR) systems, pharmacies, lab networks, and payer portals without forcing workarounds. HIPAA applies not only to covered entities within healthcare but also to their business associates, who need to uphold HIPAA protections as well.
Supporting industry standards and APIs makes identity flows consistent across platforms, enabling care teams, patients, and partners to connect without compromising security.
Federated logins and delegated access models can help control vendor permissions.
Support native mobile authentication
The mobile health market (mHealth) is booming, expected to hit $296B by 2032. Healthcare apps must offer native, low-friction authentication that feels seamless across iOS, Android, and mobile browsers. Whether it’s biometric login or deep linking to native flows, poor mobile auth UX should never hold back engagement.
Offer self-service identity administration
From resetting a password to registering a new device or managing account preferences, patients and partners should be able to manage their identities without relying on support. Embeddable UI components help healthcare organizations deliver a consistent, secure UX across every touchpoint—and across the user lifecycle, including on- and off-boarding.
Strengthen IAM with governance and policy controls
Healthcare IAM is an effective way to address and mitigate many privacy and compliance concerns facing covered entities and other stakeholders. But to get the most out of it, healthcare teams should prioritize elements of governance like policy design and enforcement.
Per the compliance experts at HIPAA Journal, one of the most important parts of impactful healthcare IAM is “access governance.” This refers to underlying protocols that determine how, when, and why access is granted or revoked across RBAC, ABAC, ReBAC, and other systems.
Healthcare IAM that’s effective and simple
In healthcare, where patient trust, compliance, and seamless access are all mission-critical, a modern IAM approach is no longer optional; it’s foundational. Healthcare IAM enables sound operations that ensure safety and security alongside quality care and optimal health outcomes. Protecting sensitive data while enabling secure collaboration across patients, providers, and partners requires authentication and authorization flows that are both airtight and user-friendly.
Descope helps teams avoid building and maintaining this IAM complexity in-house. Instead of hardcoding auth logic, developers can define authentication flows, consent rules, and fine-grained authorization policies visually—and update them without redeploying their apps.
Our drag & drop CIAM platform for healthcare supports passwordless authentication, consent-based access, mobile-native flows, and federated authentication across third-party systems, so you can secure every user interaction without compromising experience or compliance. Organizations like GoodRx, Owens & Minor, and Collabrios Health use Descope to improve customer onboarding, enhance security against identity attacks, and save developer time on building and maintaining authentication plumbing.
Get started with a Free Forever Descope account, or book a demo to see how we can support your IAM strategy.