Table of Contents
Stop sharing human credentials with AI agents
Gartner published IAM Adapts to Secure and Enable AI Agents in January 2026 as part of its Top Cybersecurity Trends series. The report examines how identity and access management (IAM) capabilities need to evolve as organizations deploy more AI agents, and where existing practices fall short. Download a complimentary copy of the report by clicking the link below.
Gartner Report: IAM Adapts to Secure and Enable AI Agents
Get strategic and implementation-oriented guidance for agentic identity.
Get copy
The central finding of the Gartner report is one we’ve been seeing across our own customer base: IAM maturity for AI agents is unevenly developed, with some areas significantly lagging behind. While capabilities like authentication and monitoring are relatively ready, other functions like identity registration, credential management, and authorization are not.
This blog shares our reflections on the report’s insights, key themes, and recommendations, and how they align with the Descope Agentic Identity Hub.
Stop sharing human credentials with AI agents
In the report, Gartner says:
“Prohibit sharing of human credentials with AI agents. Require unique identities with accountable human owners for every agent.”
Gartner reinforces this recommendation throughout the report, stating that:
“Cybersecurity leaders should require that all agents authenticate as themselves and prohibit human credential sharing or session reuse by agents.”
We believe this recommendation is as much about security as it is long-term sustainability and compliance. As the report describes in one of its strategic planning assumptions:
“By 2028, 90% of organizations that allow humans to share credentials with AI agents will have to make a significant investment to undo this design due to security and compliance issues.”
In real-world scenarios surfaced by both headlines and security organizations, the evidence for why this matters is mounting. GitGuardian’s 2026 State of Secrets Sprawl Report found over 28 million new secrets exposed in public GitHub commits in 2025, a 34% year-over-year increase. Over 1.2 million of those were AI-driven service secrets, growing 81% year-over-year.
And while exposed secrets are multiplying in the agentic era, the reality is that otherwise innocuous agents can surface credentials that organizations aren’t even aware of, then use them without human intervention. In a widely publicized incident in April 2026, an AI agent found an API token in an unrelated file that had blanket permissions, including destructive operations. It authenticated against a legacy (but operational) endpoint and deleted a production database, along with volume-level backups, in nine seconds.
In our view, human credential sharing is the single most critical mistake an organization can make when deploying AI agents. It weakens the identity boundary between human and machine, making it impossible to scope, audit, or revoke agent access independently. The fix for this, however, is found with fundamental agent identity and security architecture, not just a process or policy.
The Descope Agentic Identity Hub addresses agent credential management through OAuth 2.1-based consent and delegation. The user authorizes the agent through a consent flow, the agent receives its own scoped credentials linked back to that user, and the credential vault (Descope Connections) ensures agents never handle raw tokens directly. This allows downstream services to determine both who the agent is acting for and what it’s permitted to do, without the agent ever holding the user’s actual credentials.
For sensitive operations, scope-aware step-up authentication provides an additional layer of security before showing a consent screen. In these scenarios, the Descope Flow can inspect the scopes requested in the authorization URL before asking the user for consent: if these include permissions that require step-up, it can branch to require an additional authentication factor.
Register agents as first-class identities
We believe the Gartner report points to identity registration as one of the least mature IAM capabilities for AI agents, and here they make a careful distinction:
“Discovery alone cannot reveal why an agent exists or who is accountable; only registration processes provide this clarity.”
The report offers three implementation patterns to resolve this: integrating with existing AI governance tooling, using identity governance and administration (IGA) solutions for workforce-facing agents and using Customer Identity and Access Management (CIAM) solutions for customer-facing agents, and adding visibility requirements to credential issuance.
Our view: Gartner’s recommendations seem acutely aware of how building bespoke agentic identity is a tall order even for large enterprises. The practical reality is that most organizations lack a centralized view of what agents exist in their environment, who owns them, and what they’re authorized to do.
Our survey of over 400 identity decision-makers found that, while 88% of organizations use or plan to use AI agents, 46% of respondents cite their engineering team not having the required time or expertise to build and manage agentic identity systems. When we consider that only 37% have progressed beyond the pilot stage for their AI project, managing agent identities surfaces as a crucial part of the bottleneck.
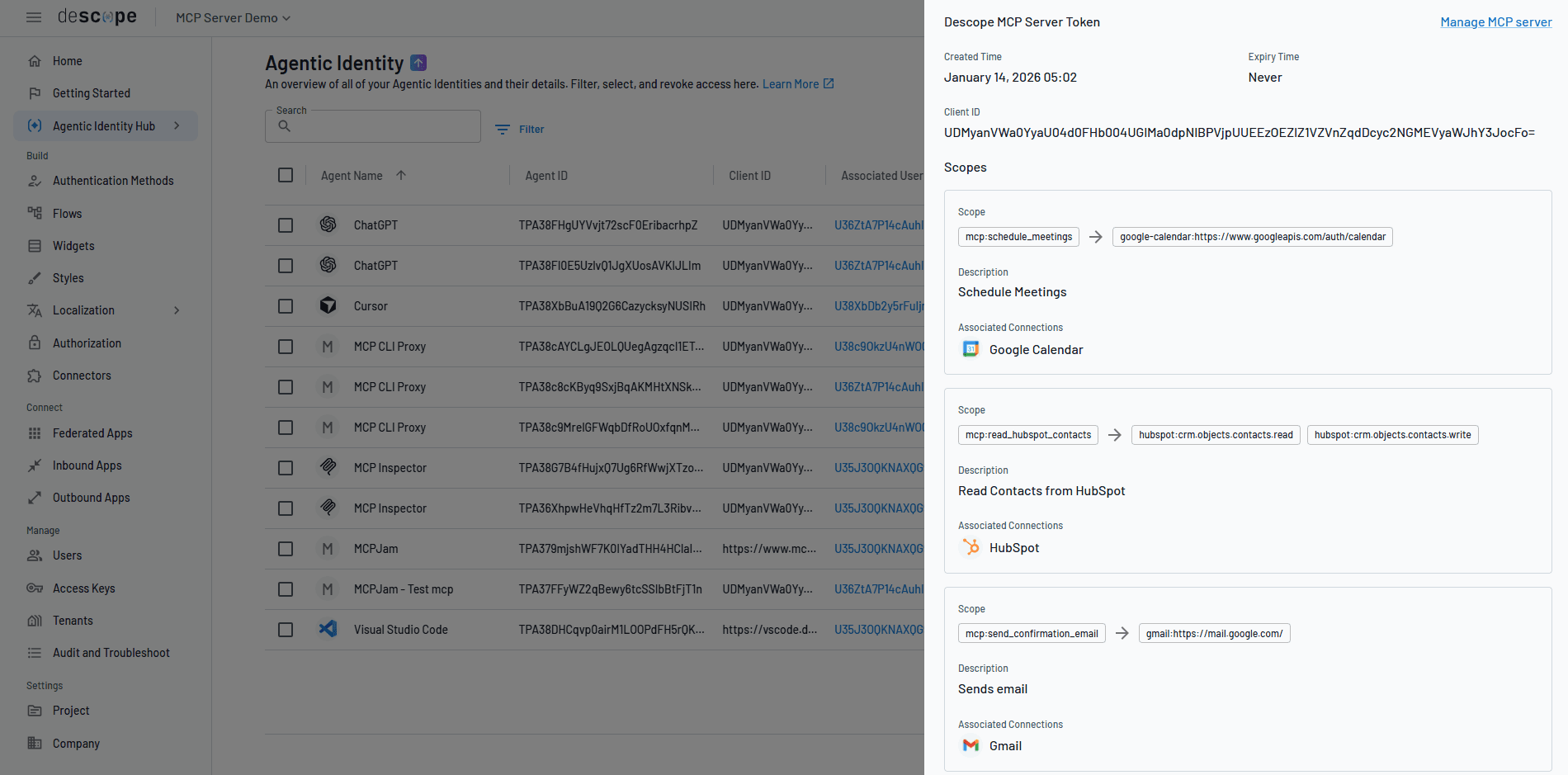
The Agentic Identity Hub provides dedicated identities for each AI agent alongside attributes, including the associated user, tenant, tool-level scopes, OAuth client ID, and registration method (Dynamic Client Registration, Client ID Metadata Documents, or manual). Security teams can view, filter, manage, and revoke agent identities from a single control plane. We believe this aligns with the long-term outlook Gartner perceives: agent identity registration as a first-class function in the identity platform itself.
Secure MCP servers and agent-to-API access
The Gartner report recommends that organizations “integrate AI-specific protocols such as Anthropic’s Model Context Protocol (MCP) to structure interactions between agents and external resources.” It also recommends:
“Register each AI agent as an OAuth client with a unique identifier and secret, manage agent access through tokens that have clearly defined scopes, and implement delegated authority so human users explicitly authorize agents to act on their behalf using standard OAuth consent flows or administrative approval mechanisms for higher-risk actions.”
In our view, the gap between what the MCP auth spec recommends and what developers actually implement remains quite wide. Knostic research in 2025 found nearly 2000 MCP servers on the open internet with no security at all. Every threat on the OWASP Top 10 for Agentic Applications cites identity-related remediations, yet most MCP server developers visibly lag behind best practices.
Our conclusion is that this is due to just how many unfamiliar requirements the MCP spec mandates: OAuth 2.1 with Proof Key for Code Exchange (PKCE), DCR/CIMD, Protected Resource Metadata, Resource Indicators, and many other mechanisms that are niche even within the auth vertical. These requirements represent a substantial engineering burden for teams whose primary focus is building agentic functionality, not identity infrastructure.
The Agentic Identity Hub helps MCP developers by offloading this burden to a comprehensive auth and access control layer for MCP servers, securely connecting MCP servers (and any third-party tools these MCP servers connect to) with AI agents via protocol-compliant OAuth 2.1 flows.
Organizations can safely expose their MCP servers to MCP clients with OAuth 2.1 and PKCE, validate access with user authentication and consent management, support context-aware client registration (DCR/CIMD) with agent risk assessment flows, and assign granular per-agent and per-tool scopes. Descope acts as the dedicated authorization server for each MCP server with discovery endpoints, well-known URIs, and all the niche but necessary plumbing the spec requires.
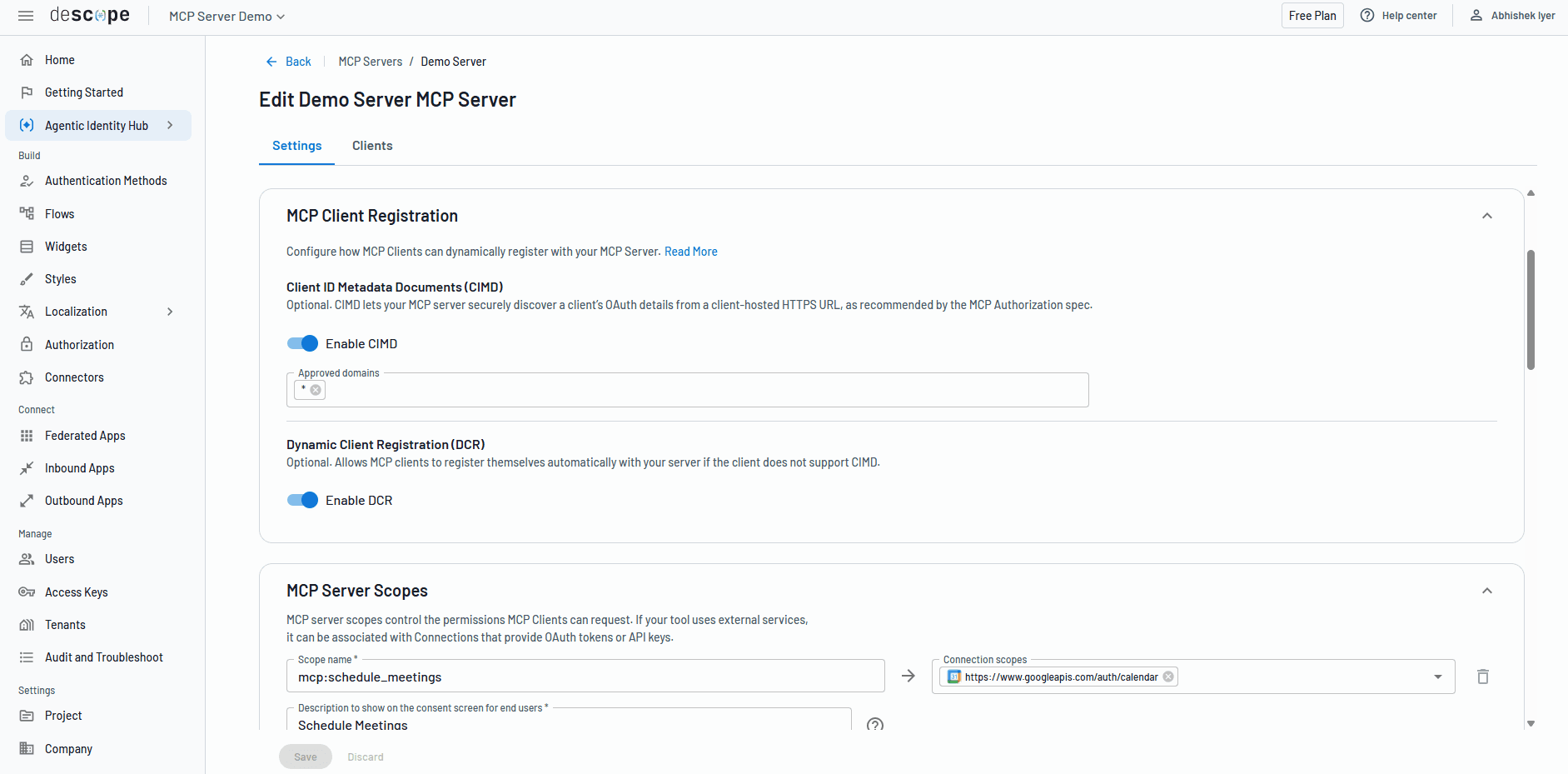
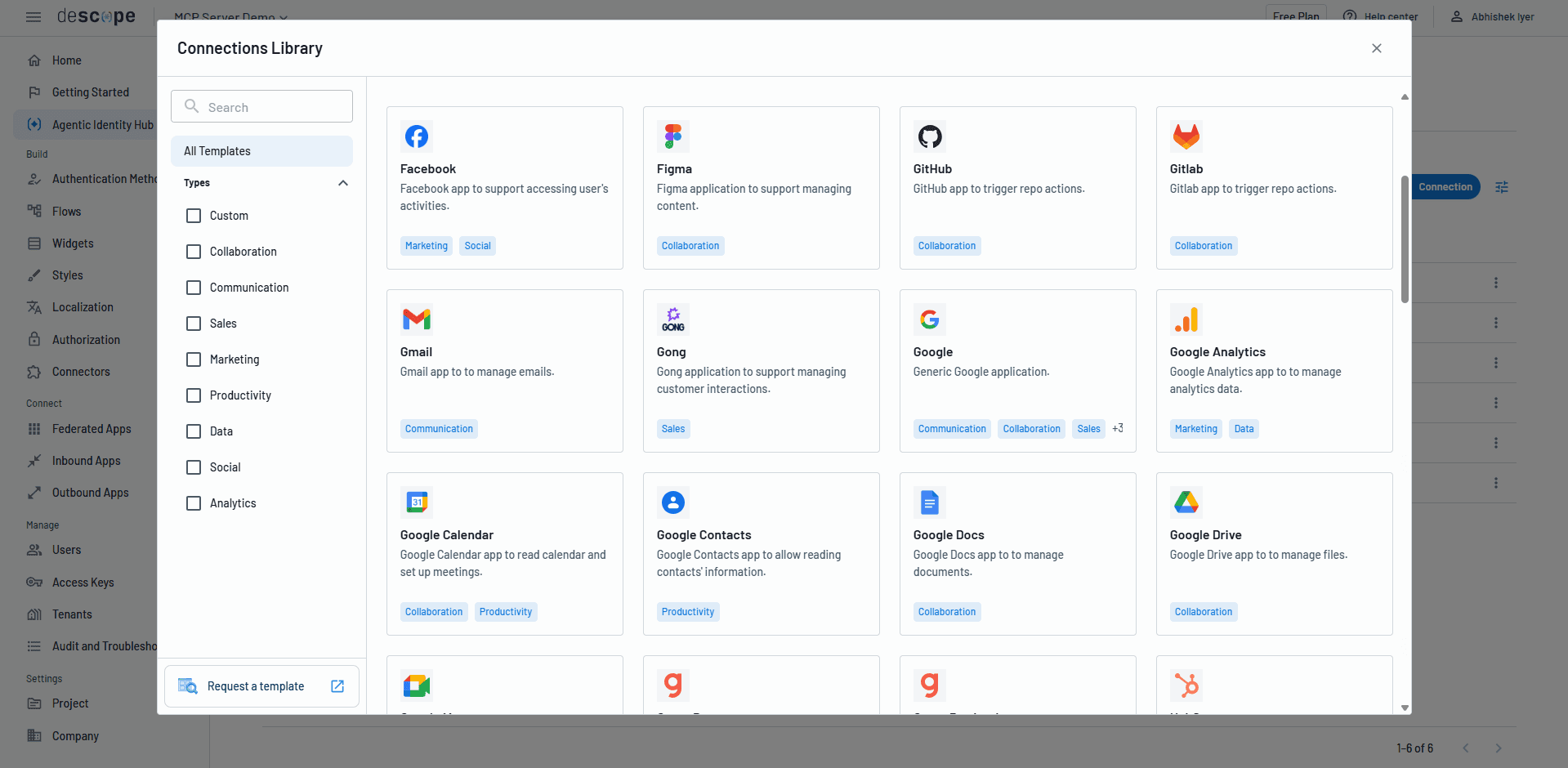
For agents that need to connect with downstream services, Descope Connections acts as a credential vault, and provides 50+ prebuilt integration templates.
Enforce least privilege through policy-driven authorization
Gartner rates authorization maturity as “Poor” in the average implementation and recommends prioritizing a “robust agent identity process as the foundation for improving authorization controls.” The report also recommends that organizations “increase the priority of authorization improvements across all actor types, not just AI, since autonomous agents can more easily exploit excessive permissions.”
In our view, this traces a direct line back to one of the report’s central planning assumptions:
“Through 2029, over 50% of successful cybersecurity attacks against AI agents will exploit access control issues, using direct or indirect prompt injection as an attack vector.”
The connection Gartner draws between identity registration and authorization is of dire importance to organizations deploying agents in the current security landscape. Without knowing what an agent is, who authorized it, and what it’s supposed to do, authorization policies have nothing meaningful to evaluate against. This is, in our view, why the report positions identity registration as a prerequisite rather than a parallel effort.
It’s our view that Descope’s Agentic Identity Hub satisfies Gartner’s recommendations by providing enterprise-grade policy controls that can define granular authorization rules governing which AI agents can access MCP servers and which tool-level scopes they’re allowed to invoke. Policies can take context from the user, tenant, MCP server, agent, JWT claims, and downstream service into account.
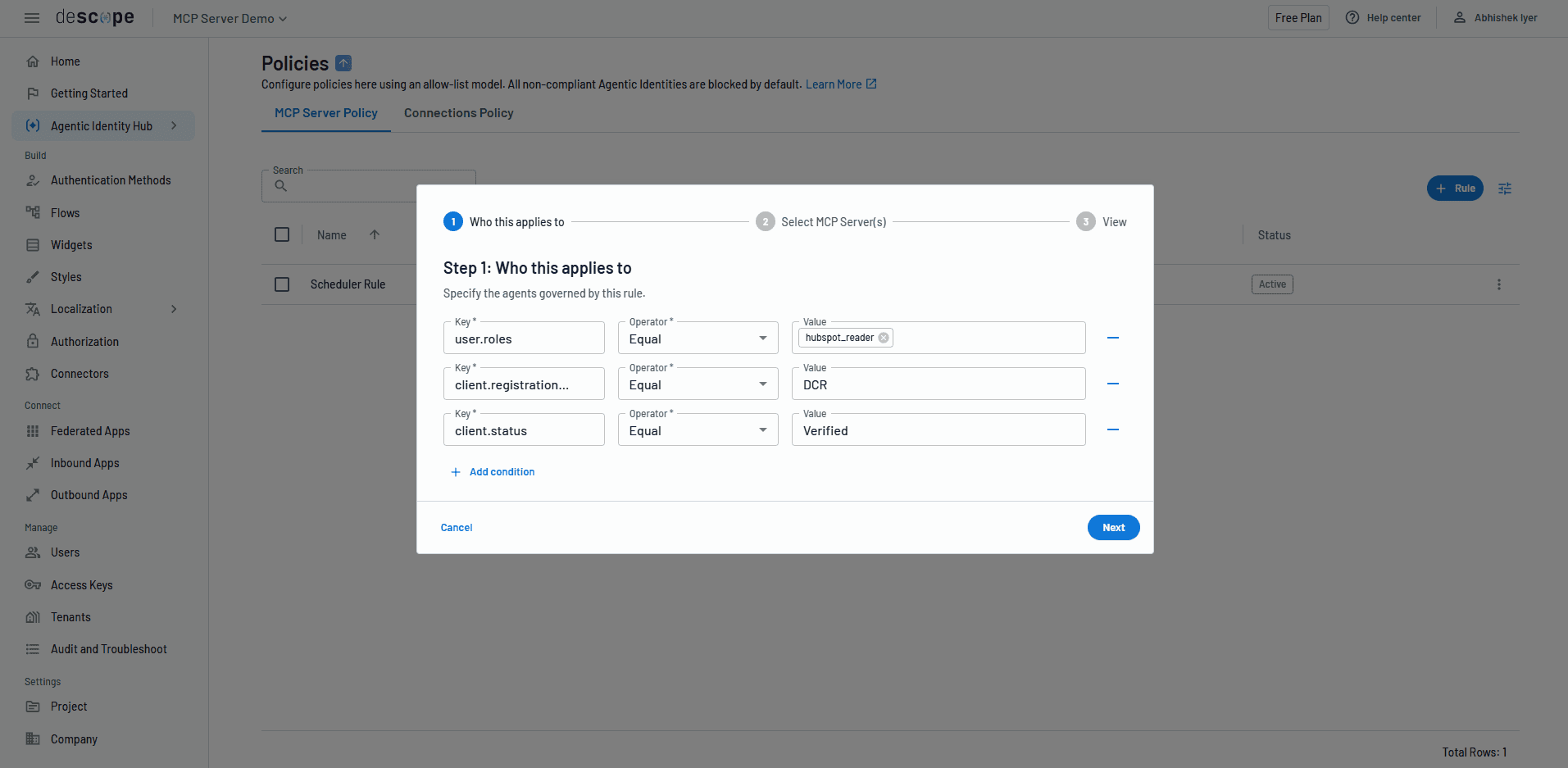
Agents receive short-lived, scoped credentials tied to the minimum permissions defined by access policies. For sensitive operations, step-up authentication requires explicit human verification before the agent can proceed. Every action is logged and exportable to any Security Information and Event Management (SIEM) provider, creating an observable chain of accountability from agent action back to the delegating user.
Choose a platform that handles both workforce and customer agents
In the report, Gartner says:
“Include workforce-facing AI in the existing workforce IAM strategy and toolset, manage customer-facing AI through CIAM strategy and tools, and Avoid combining customer identity data with workforce identity data in highly regulated industries where this is prohibited.”
We agree with the regulatory separation principle: customer and workforce identity data often carry different compliance requirements, and some industries prohibit commingling them.
Where we see it differently from the report is the suggestion to pursue discrete tooling. In our view, the split between workforce agents and customer agents introduces friction at a chokepoint where agility and developer experience matter enormously for agentic deployment. Agent scenarios often don’t fit cleanly into the workforce/customer binary: a customer-facing AI agent might need access to internal tools via MCP to fulfill a request, while an internal agent might need to access customer-facing services to complete its task.
We believe organizations should choose a platform that can handle both use cases within a single, unified identity architecture, provided it supports the tenant isolation and data separation that regulation requires. The Agentic Identity Hub can cater to both external and internal-facing MCP servers within the same platform. Organizations can plug into their existing identity stack using single sign-on (SSO) and System for Cross-Domain Identity Management (SCIM) for internal-facing agents while managing customer-facing agentic identities through Descope’s CIAM functions.
The Bring Your Own Auth (BYOA) capability lets organizations keep their existing identity system as the source of truth while Descope acts as the OAuth authorization server for their MCP servers, whether through identity federation via OpenID Connect (OIDC) or Security Assertion Markup Language (SAML) or direct token exchange. This provides a single control plane for agentic identity policy, monitoring, and lifecycle management regardless of deployment context, while maintaining the data separation that, in our view, Gartner is recommending.
How Descope aligns with Gartner’s recommendations
The table below examines how Descope’s capabilities cleanly line up with the recommendations in this Gartner report, from credential management to authorization and policy enforcement.
Gartner recommendation | Descope Agentic Identity Hub |
|---|---|
Prohibit human credential sharing; require unique agent identities with accountable human owners | • Dedicated agent identities linked to human users via OAuth-based consent and delegation • Agents never hold the user’s primary credentials |
Implement standardized process for AI identity registration with purpose and intent visibility | Centralized agentic identity management with attributes: associated user, tenant, tool-level scopes, OAuth client ID, and registration method |
Automate credential management through shared authentication services and federation | • Credential vault (Descope Connections) manages OAuth tokens and API keys • Bring Your Own Auth supports existing identity providers via OIDC/SAML federation • 50+ prebuilt integration templates for third-party tool access |
Register AI agents as OAuth clients with unique identifier; manage access through scoped tokens | • Each agent registered as an OAuth client with dedicated identity • Per-agent and per-tool scopes with short-lived, ephemeral credentials |
Integrate MCP; use proxies for centralized policy enforcement | • Comprehensive MCP auth implementation: OAuth 2.1 + PKCE, DCR/CIMD, per-tool scopes, tenant isolation • Descope serves as the dedicated OAuth authorization server for MCP servers |
Implement delegated authority with OAuth consent flows | • User consent flows with configurable authentication steps • Agents receive scoped credentials tied to explicit user authorization • Step-up auth (human-in-the-loop) for sensitive operations |
Enhance authorization controls for least privilege enforcement | • Unified policy layer with per-agent, per-tool, per-tenant authorization based on user roles, JWT claims, agent type • Step-up auth for sensitive actions |
Extend monitoring/observability into AI architecture | • Full audit logging of agent actions exportable to any SIEM • Visibility into agent identity, scopes, tool access, and policy enforcement from a single dashboard |
Update strategies for workforce vs. customer-facing AI | • Single platform supports both internal and external MCP servers • SSO/SCIM federation for workforce use cases, CIAM for customer-facing • Bring Your Own Auth and federation preserve existing identity provider semantics |
Start building on top of secure agentic identity foundations
The Gartner report makes, what is in our view, a clear case that purpose-built identity management for AI agents is a present-day requirement and not a future-tense investment. The uneven maturity of implementations already in production means most organizations have specific work to do in identity registration, credential management, and authorization. But those that get this right from the earliest possible point will avoid the rework Gartner predicts for credential-sharing schemes, positioning themselves to scale agentic deployments without holding back due to accumulated technical debt.
The Descope Agentic Identity Hub is designed specifically to address the gaps this report underlines: agent identity as a first-class type, OAuth 2.1-based delegation instead of sharing human credentials, comprehensive MCP auth, policy-driven authorization with context awareness, and full visibility across the entire agentic lifecycle.
Any developer can start using the Agentic Identity Hub today by signing up for a Free Forever Descope Account. See agentic use cases in action now and sign up to get started. Have questions or a specific project you’d like to discuss? Reach out to our auth experts and join the AuthTown dev community to connect with like-minded builders.
FAQs about IAM adapting to secure and enable AI agents
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner's research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.